
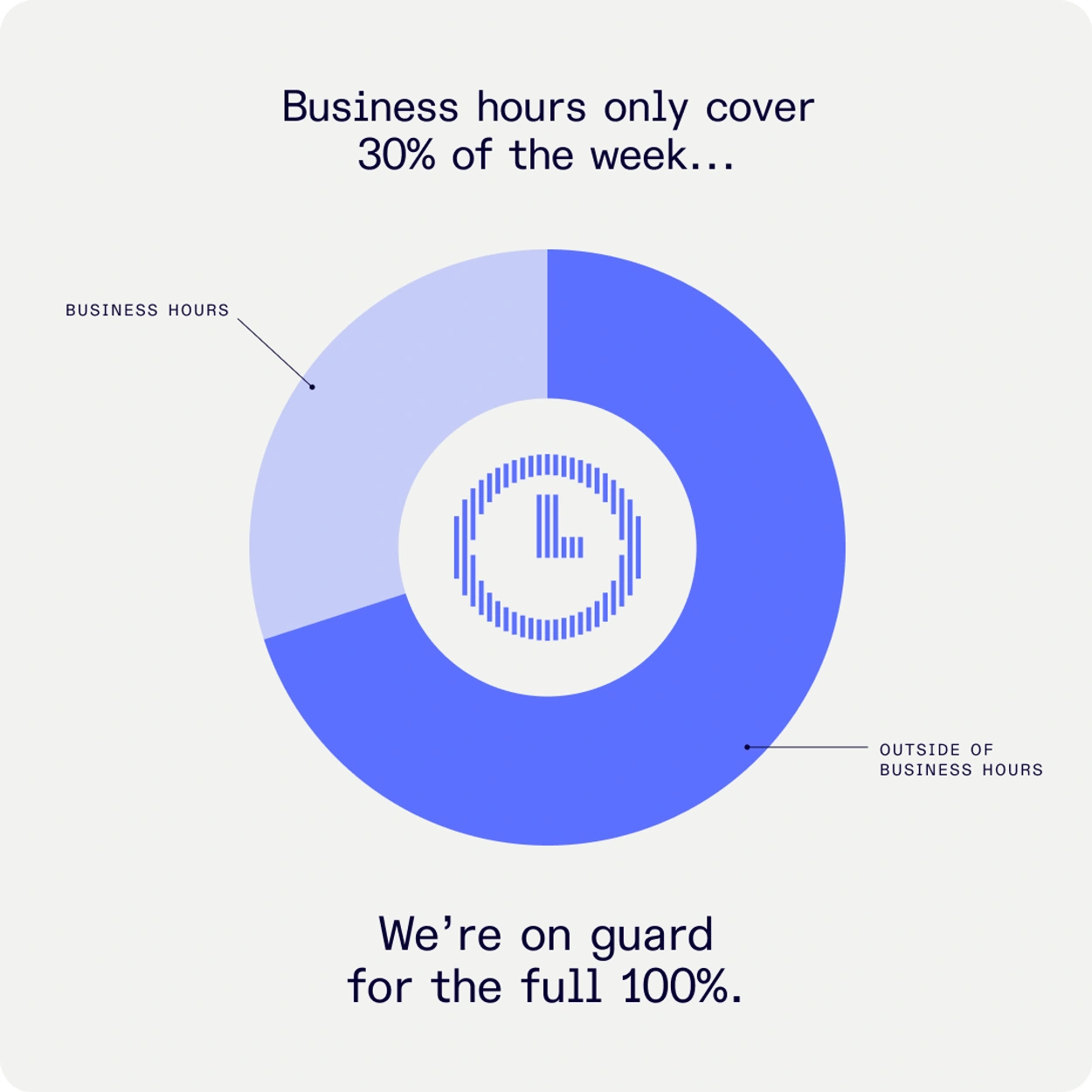
In a cyber incident, every minute counts. We are available 24/7.
✓ Immediate deployment - 24/7 availability without waiting
✓ IT and OT forensic investigation under one roof
✓ From initial containment to full recovery and stronger security
Are you currently dealing with an incident? Call immediately: +31 (0)88 733 13 37
A cyber incident — ransomware, data breach, targeted attack — is no time for a quotation process. DEFION's incident responders are available 24 hours a day, 7 days a week for immediate deployment. We limit damage, preserve evidence, and bring your organization back to operational status in a controlled manner.
When speed is everything
In a cyber incident, every minute of delay increases the damage. Attackers move within your environment, destroy traces, and embed themselves deeper. On average, it takes organizations 194 days to detect a breach. By the time an incident becomes visible, the attacker has usually been active for a long time.
Without a structured, immediate response, you risk:
- Further spread of ransomware or malware through your network and to your backups
- Loss of forensic evidence crucial for root cause analysis and legal actions
- Incorrect or delayed communication that damages the trust of customers, partners, and regulators
- Insufficient insight into the attacker’s methods — making recurrence inevitable
- Non-compliance with reporting obligations (NIS2, GDPR, DORA) with associated fines and liabilities
DEFION Incident Response ensures rapid containment, in-depth analysis, and controlled recovery.
What DEFION Incident Response concretely offers
Our incident responders combine technical expertise with crisis coordination:
✔ Rapid triage - Immediate assessment of the nature, scope, and urgency of the incident by an experienced Incident Handler
✔ Containment - Isolating and stabilizing affected systems - stopping the spread
✔ Forensic investigation - Collecting and analyzing evidence, timeline reconstruction, root cause and security analysis
✔ Impact and damage analysis - Which data, systems, and users are affected?
✔ Attacker profiling - Who are you dealing with, what do they want to achieve, which methods do they use, what can we expect?
✔ IT and OT scope - We investigate both IT environments, devices as well as industrial OT networks and SCADA systems
✔ Mitigation and recovery advice - Concrete steps to prevent recurrence
✔ Communication guidance — Support with internal communication, customer notifications, and legal obligations
✔ Management reporting — Management summary for executives, regulators, and cyber insurers
✔ Lessons learned — Debriefing with your team to structurally prevent recurrence
Incident Response Retainer - be prepared before things go wrong
For organizations with critical processes or an elevated threat profile, we offer an Incident Response Retainer. This gives you:
✔ Guaranteed priority - Immediately deployable, no queue, no capacity issues at the crucial moment
✔ Pre-agreed procedures - Contact, escalation, roles, and authorities are established before things go wrong
✔ Response time guarantee - Initial diagnostics within 30 minutes; first responder on site within 2-4 hours
✔ Periodic tabletop exercises - Your team practices the procedures annually in a simulated scenario
✔ Lower hourly rates - Our retainer clients pay a reduced rate upon deployment
✔ Designated contacts - You don’t call a general number but your fixed DEFION contacts
A retainer means: no chaos when things go wrong.

How incident response works at DEFION
-
Detection & initial analysis
First report via our 24/7 hotline. Our duty officer immediately assesses the nature, urgency, and initial scope of the incident. -
Containment & stabilization
We isolate affected systems, block further spread, and stabilize the environment — as quickly as safely and responsibly possible. -
Forensic investigation
Controlled collection of forensic evidence. Timeline reconstruction of the attack: when it started, how the attacker moved, which data was accessed? -
Recovery & hardening
Guidance on system restoration, validation of mitigations, and recommendations to close attack vectors to prevent recurrence. -
Reporting & debriefing
Technical final report plus executive summary. Personal debriefing with your team. Concrete lessons learned to structurally improve your resilience.
For which organizations is incident response essential?
Immediate incident response is critical for:
- Organizations with business-critical digital processes where downtime is very costly or life-threatening
- Organizations in regulated sectors with reporting obligations: financial (DORA), healthcare, energy, government (NIS2), GDPR
- Organizations with an elevated threat profile: critical infrastructure, manufacturing, OT environments
- Organizations that want preparation — so there is no chaos when things go wrong
- Organizations where an incident has immediate reputational impact on customer trust or shareholder value

"Thanks to DEFION, we benefit from up-to-date knowledge about current security threats and ways to prevent risks. We have peace of mind knowing that we are fully supported 24/7 by their team." AFAS Software
"Thanks to DEFION, we benefit from up-to-date knowledge about contemporary security threats and means to avert risks. We have peace of mind knowing we are fully supported 24/7 by their team.”
Jeroen van Stokkum Manager ICT
![[object Object]](https://assets.defion.security/api/assets/images/l7GY2Z9ip58BiQ5Bckyaz6f4Kz3KdM-w2000.webp?t=3840)
“The sector and the partners we work with maintain increasingly high security standards for IoT-products and services. Protecting the privacy of individuals in the images and the sensitivity of the information the drones collect, such as on objects in critical infrastructure, requires our security to be airtight. With Defion, we are working with a professional partner who can support us at the right level. The collaboration also fits perfectly within our strategy to deliver reliable and secure drone technology to European customers.”
Benjamin van der Hilst Co-Founder & CEO

“New requirements from NIS2 for OT systems are increasing the focus on security. With Defion, we know we have the right expertise in-house to keep our systems secure. The collaboration was easy and pleasant; the specialists truly sat next to us rather than across from us. Thanks to their openness and expertise, we are working together toward the same goal: optimal security. This gives us the confidence to face the future.”
Alexander OdijkTeam Manager

“If you look at where we were ten years ago, we’ve made enormous progress. The sense of control is greater. With Security Assurance and MDR we have set up processes and control mechanisms that allow us to limit the impact of a potential attack. The collaboration also serves as a constant reminder to maintain focus on security and set the right priorities in that area. It keeps us alert and sharp. Moreover, Defion’s specialists are highly technical and passionate about their field. That clearly shows in their services.”
Gerco VermeerDevelopment Manager

Frequently Asked Questions
Can we call you directly now if we have an incident?
Yes. +31 (0)88 733 13 37 is staffed 24/7. Our Incident Handler answers immediately and starts the triage.
How much does incident response cost?
Ad-hoc deployment is charged on an hourly basis. A retainer offers fixed priority and lower rates. An introductory conversation about a retainer is always free of charge.
What if it turns out to be a false alarm afterwards?
No problem. We diagnose first. We assess quickly and scale down depending on the severity and urgency. Better to escalate too quickly than to fall behind the facts later.
Do you also perform forensic investigations on OT environments?
Yes. We have specialists with specific OT/SCADA knowledge who can forensically investigate industrial environments — with attention to safety and operational continuity.
Can we use the report for our cyber insurer?
Yes. Cyber insurers expect a forensic report for claims. We prepare our reports with that application in mind. You decide whether or not it is shared.
What are our reporting obligations in case of an incident?
That depends on your sector and the nature of the incident. We advise you on the NIS2 reporting obligation (Cybersecurity Act), GDPR data breach notification to the Data Protection Authority, and requirements from DORA for the financial sector.
How do you help us prevent it from happening again?
Our report always contains a section with concrete improvement measures. Upon request, we also advise and test during implementation - or offer our MDR service for continuous monitoring.
Do you have an incident now - or do you want to be better prepared?
Incident? Call immediately: +31 (0)88 733 13 37 (24/7)
Retainer or preparation? Schedule a conversation now!
- Compromise Assessment
Many breaches remain undetected for months, silently eroding trust and value. DEFION’s Compromise Assessment gives executives clarity by answering a critical question: are we already compromised? Through advanced threat hunting, forensic analysis, and review of network and endpoint activity, we uncover hidden attacker presence and indicators of compromise. Leadership gains fact-based assurance — or an urgent call to action — to protect the business and safeguard reputation.
- Incident Response Services
Incident Response is how you regain control when a cyberattack hits. When it does, it’s not just your IT but your operations, customers, and reputation are at stake. DEFION helps you take control fast: contain the threat, investigate what happened, and recover critical systems. We guide you through every step.The goal: reduce impact now, and build stronger resilience for what comes next.
- Incident Response Table Top
In a cyber crisis, leadership decisions determine the outcome. DEFION’s Incident Response Tabletop Exercise brings executives, management, and security teams together in a safe but realistic simulation of a major incident. By walking through response scenarios, we help leadership validate decision-making, clarify roles, and strengthen communication. The result: board-level confidence that the organization is ready to respond effectively when it matters most.
- Digital Forensics
When a security breach unfolds, there’s no room for hesitation. Our Incident Response team goes straight to the root cause, containing threats and neutralizing attackers with precision. By restoring control quickly and protecting your most critical assets, we help your organization move from chaos to confidence — minimizing damage, cost, and downtime.
- Incident Response Retainer
When every minute counts, hesitation is costly. An Incident Response Retainer ensures your organization has immediate access to seasoned cybersecurity experts, ready to contain, investigate, and neutralize threats before they escalate. With a proactive retainer in place, you gain predictability, priority response, and the confidence that your business can withstand and recover from even the most critical incidents.
- Incident Response Readiness
When a cyber incident strikes, the difference between disruption and resilience lies in preparation. DEFION’s Incident Response Readiness Assessment equips executives with a clear understanding of how prepared their organization truly is. By testing processes, communication lines, and decision-making under realistic scenarios, we help leadership identify gaps, strengthen playbooks, and ensure the organization can respond with speed and confidence.

Turn 24/7 security monitoring into real response capability.
Speak with our experts and learn how rapid, expert-led response transforms your security posture.
Contact usContact us