
Have a pentest performed
Discover where your organization is truly vulnerable
-
Manually tested - no false positives
-
Grey box standard, OT experience available
-
Retest included after remediation
Compliance reports state what is correct on paper. A pentest shows what an attacker can actually do in practice.
DEFION performs penetration tests for organizations where downtime, data loss, or reputational damage is not an option. Independent, without vendor lock-in, by senior ethical hackers with years of practical experience.
One vulnerability is enough
Attackers do not look for all weak spots. They look for one entry point.
Many organizations rely on compliance, tooling, or internal controls - and discover too late that the actual resilience is different than assumed. A pentest makes that difference visible before someone else does.
A DEFION pentest gives you insight into:
- Which vulnerabilities exist and how they can concretely be exploited
- Which attack paths an attacker can follow - including combined attacks
- What the impact is on your business operations, data, and reputation
- Which improvement actions deserve priority for security, IT, and development teams
Our approach: manual, methodical, context-driven
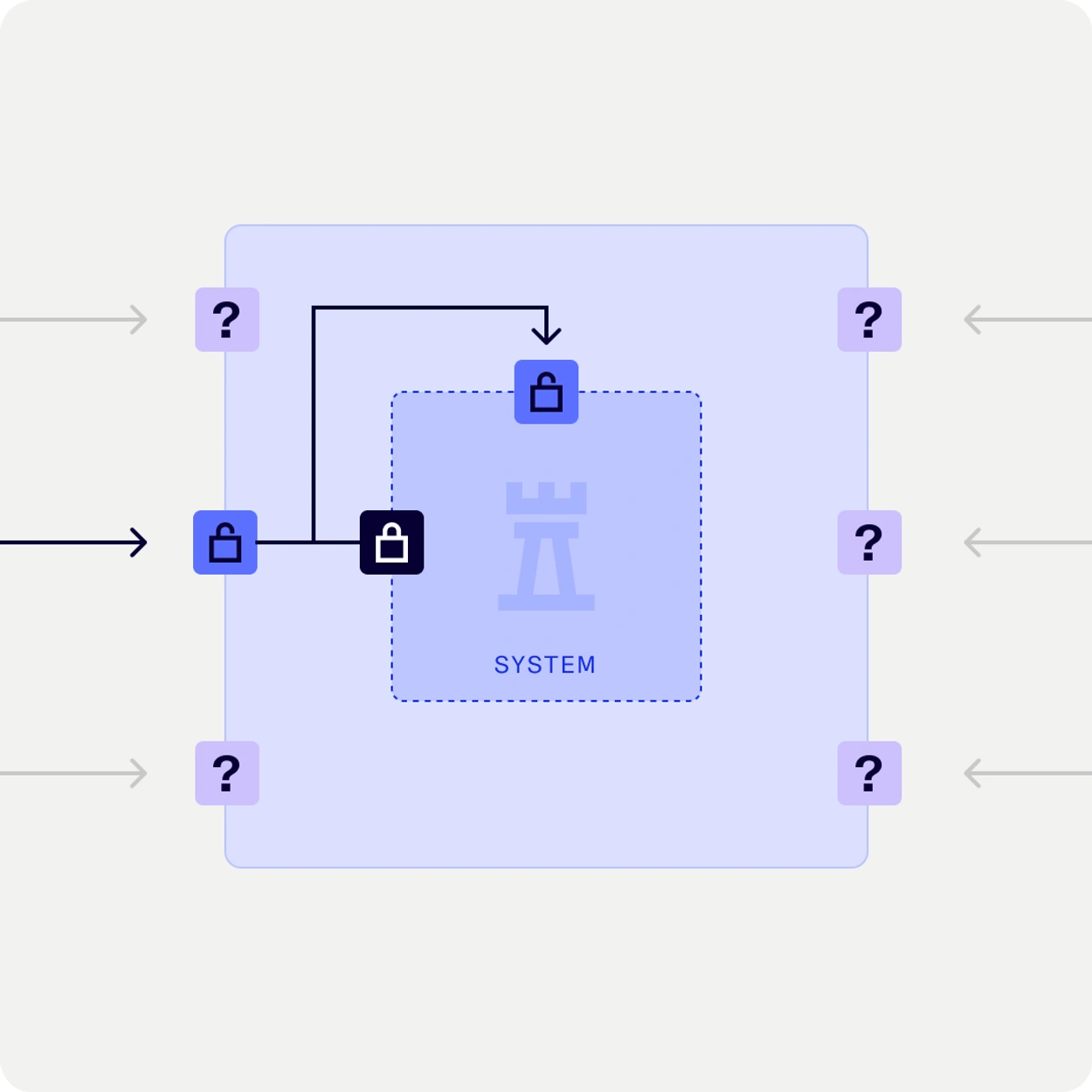
Automated tools find known patterns. Our specialists find what tools miss. DEFION pentests are largely performed manually. Our ethical hackers use experience, logic, and creativity to provide a realistic picture of vulnerabilities that an attacker could actually exploit. All output from automated tooling is manually verified - no false positives in your report.
Our standard is grey-box: we test from the perspective of both an unauthenticated and an authenticated user. This provides the most realistic view of your attack surface. Findings are assessed against established standards such as OWASP Top-10 and NCSC guidelines, supplemented with DEFION's own research experience built up over more than twenty years of pentesting. This guarantees that all known vulnerabilities are always checked.
What a DEFION pentest concretely delivers to you
- Realistic attack simulation by experienced ethical hackers
- Insight into vulnerabilities and how they can be combined or exploited
- Risk prioritization based on your specific business context and impact
- Report at both technical and management levels — without unnecessary noise
- Concrete improvement actions, directly applicable for your teams
- Re-test after remediation possible — so you can be sure it is closed

20+ years of penetration testing in practice
DEFION (originating from Computest Security and Incide) has been conducting penetration tests for organizations in critical sectors for more than two decades. That experience is present in every test - not only in the method but in the judgment of the specialist behind the keyboard.
Our ethical hackers hold recognized certifications including OSCP, OSWE & OSEP. All specialists have a Certificate of Conduct and are bound by strict confidentiality.
Which pentest suits your situation?
Depending on your IT landscape and objectives, we perform different types of tests:
Web Application Pentest
Thorough testing of web applications and APIs according to OWASP and CVSS. Grey-box as standard, black- or white-box on request. For organizations with customer portals, SaaS products, or critical web environments.
Internal Pentest
Simulation of an attacker who is already inside - via a compromised employee, supplier, or device. The Active Directory is assessed for permission structure, presence of weak passwords, and possibilities for lateral movement. Additionally, we perform an assessment of the Microsoft 365 environment (configuration, access rights, and possible data exposure), the WiFi networks and virtual workplaces such as Citrix and thin clients, and the hardening of workstations and laptops based on best practices.
External Pentest
Attack simulation from the perspective of an external attacker. What is visible from the internet, which services are unintentionally accessible, and what can an attacker achieve with that? Including Leaked Credentials Analysis - are your employees' passwords from previous data breaches still usable?
OT Pentest
Controlled attack simulation on industrial environments and process control. DEFION has specifically adapted the test methodology for OT environments - to minimize impact on availability and correct operation. Prior to the test, DEFION discusses all risks with your team. Test scenarios are tailored to your specific architecture: network segmentation, authentication, supplier access, and secured components.
Cloud Security Assessment
Assessment of your cloud environment on Identity & Access Management, network security, storage configuration, security monitoring, and compliance. Including consultation with your cloud administrator to put findings into context.
Red Team Engagement
Advanced, scenario-driven attack simulation focused on your full detection and response capability. Not only technical vulnerabilities — also people, processes, and physical access.
During the intake, we determine together which approach is appropriate.

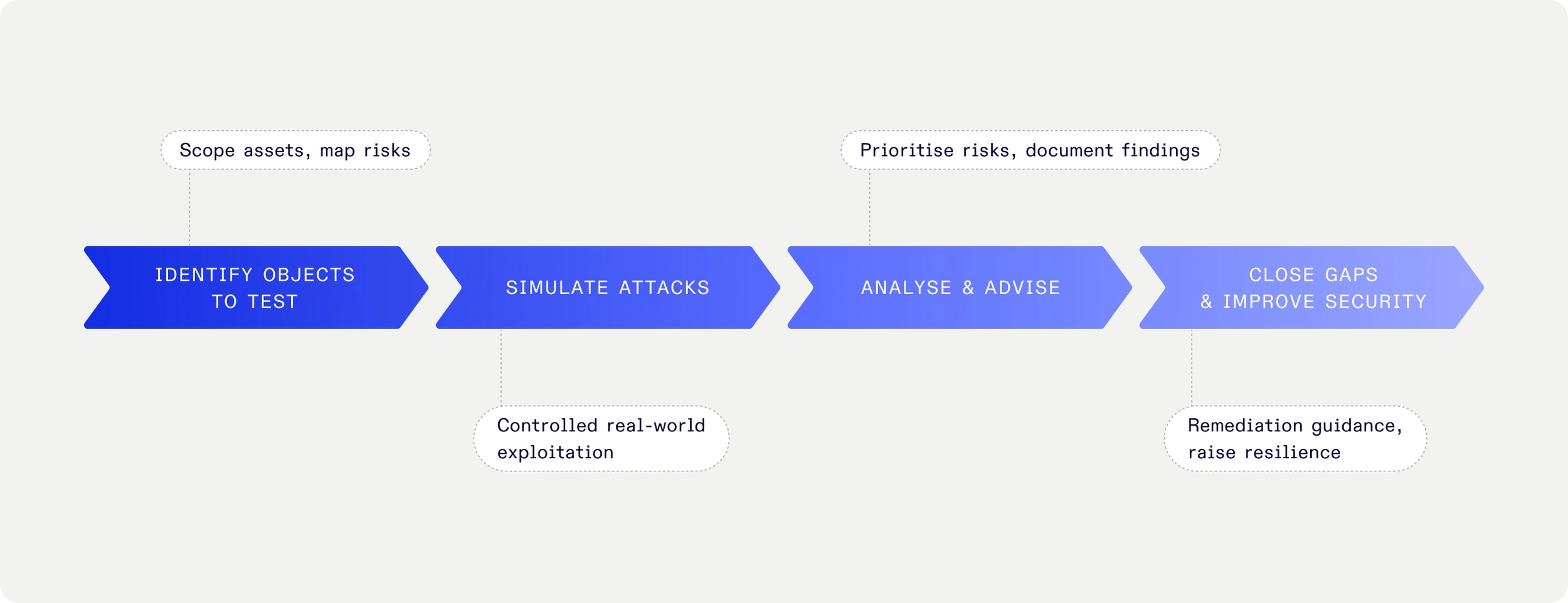
How a pentest at DEFION proceeds
-
Scope & intake: We determine objectives, systems, and conditions together. The security specialist creates a test plan with exact scope, IP addresses, URLs, and attack perspective.
-
Testing phase — Manual attack simulation by an experienced ethical hacker. Methodical and controlled — within the agreed scope, with attention to operational continuity.
-
Reporting & prioritization — Clear report with findings at both technical and management levels. Risks prioritized based on business impact. No generic list — but directly applicable insights.
-
Report discussion — Personal explanation of the findings by the executing specialist. So your team understands what was found and what should be addressed first.
-
Validation — After remediation, we retest the mitigations. So you can be sure the vulnerability is actually closed.

"With DEFION we have made enormous progress. The sense of control is greater. The specialists are very technical and passionate about their field. This clearly shows in their services." FuturumShop, e-commerce client

"Thanks to DEFION, we benefit from up-to-date knowledge about contemporary security threats and means to avert risks. We have peace of mind knowing we are fully supported 24/7 by their team.”


“The sector and the partners we work with maintain increasingly high security standards for IoT-products and services. Protecting the privacy of individuals in the images and the sensitivity of the information the drones collect, such as on objects in critical infrastructure, requires our security to be airtight. With Defion, we are working with a professional partner who can support us at the right level. The collaboration also fits perfectly within our strategy to deliver reliable and secure drone technology to European customers.”

“New requirements from NIS2 for OT systems are increasing the focus on security. With Defion, we know we have the right expertise in-house to keep our systems secure. The collaboration was easy and pleasant; the specialists truly sat next to us rather than across from us. Thanks to their openness and expertise, we are working together toward the same goal: optimal security. This gives us the confidence to face the future.”

“If you look at where we were ten years ago, we’ve made enormous progress. The sense of control is greater. With Security Assurance and MDR we have set up processes and control mechanisms that allow us to limit the impact of a potential attack. The collaboration also serves as a constant reminder to maintain focus on security and set the right priorities in that area. It keeps us alert and sharp. Moreover, Defion’s specialists are highly technical and passionate about their field. That clearly shows in their services.”
For which organizations do we perform pentests?
Our pentests are performed for all kinds of organizations in various sectors:
- With business-critical IT environments
- In highly regulated sectors, such as critical infrastructure, finance, and government
- With in-house development teams
- That want certainty instead of assumptions

Frequently Asked Questions
What is the difference between a pentest and a vulnerability assessment?
A vulnerability assessment broadly maps vulnerabilities. A pentest goes further: our ethical hackers actually try to exploit vulnerabilities to determine what an attacker can achieve. Both have their value - during the intake we advise which approach fits best.
What is the difference between grey-box, black-box, and white-box?
In black-box, the tester starts without prior knowledge — like an external attacker. In white-box, the tester has full access to documentation and source code. Grey-box is in between and generally provides the most realistic and efficient view. DEFION standardly chooses grey-box, unless your situation requires otherwise.
How long does a pentest take?
A targeted web application pentest typically takes 3–5 days. A comprehensive internal pentest or red team engagement can take several weeks. We align the duration with your schedule and objectives.
Can a pentest be used for NIS2 or ISO 27001?
Yes. A pentest provides demonstrable technical evidence of your security level - relevant for both NIS2 compliance and ISO 27001 certification and DORA requirements.
Does DEFION also perform OT pentests?
Yes, with an adapted methodology that specifically takes into account the availability and vulnerability of industrial systems. We always discuss the risks with your team in advance.
How much does a pentest cost?
The costs depend on scope, type of test, and complexity. Contact us for a tailored indication — usually we can provide an initial estimate within one working day.
An initial estimate within one working day
Schedule a scope discussion
- External Pentest
Your digital perimeter is the first thing adversaries will probe — and the first thing customers rely on. External Penetration Test simulates real-world attacks on your digital perimeter. Gain executive-level visibility of risks, validate defenses, and strengthen business continuity.
- Vendor Security Assessment
Assess and monitor the security maturity of your vendors with DEFION’s Vendor Security Assessment. Scalable, efficient, and board-ready for executive decision-making.
- Secure Development Training
DEFION’s Secure Development Training equips developers with secure coding skills to prevent vulnerabilities early in the lifecycle. Hands-on, standards-based, and tailored to your technology stack.
- Mobile App Security Assessment
Secure your iOS, Android, or cross-platform apps with DEFION’s Mobile App Security Assessment. Fast, collaborative, OWASP MASVS-aligned, and developer-focused.
- Email Risk Assessment
DEFION’s Email Risk Assessment evaluates and tests your organisation’s email security posture. Identify gaps, validate defenses, and receive actionable improvements against phishing, malware, and spoofing attacks.
- Cloud Security Assessment
With DEFION’s Cloud Security Assessment, leadership gains a clear understanding of how secure and resilient their cloud environments truly are. By assessing configurations, access controls, and exposure to evolving threats, DEFION highlights vulnerabilities that could impact business continuity and trust. Delivered with prioritized, executive-level insights, the service enables organizations to optimize cloud security investments, strengthen compliance, and maintain confidence in their digital transformation journey.
- Code Security Review
Identify vulnerabilities, logic flaws, and insecure implementations in your source code before they become risks. DEFION’s Code Security Review delivers expert manual analysis, clear reporting, and practical remediation advice to strengthen your application security.
- Internal Pentest
Cyber attackers don’t need to break the front door if they can move freely once inside. Our Internal Penetration Test gives executives a board-ready view of what an intruder could actually achieve within your environment — from accessing sensitive data to disrupting business operations.
- Web Application Pentest
With DEFION’s Web Application Penetration Testing, organizations gain clarity on the hidden risks within the digital services that drive customer engagement and business operations. By identifying vulnerabilities in web platforms before attackers can exploit them, DEFION helps leadership safeguard sensitive data, protect brand trust, and ensure business continuity. Delivered with clear, prioritized insights, our testing transforms complex technical findings into actionable guidance for executives—empowering smarter security decisions and stronger resilience.
- Red Teaming Services
DEFION Red Teaming delivers realistic cyberattack simulations to measure resilience and meet regulaatory requirements. Test detection, response, and business impact beyond penetration testing.
- Wireless Pentest
DEFION’s Wireless Penetration Test assesses WiFi security against real-world threats. Attack simulations, expert analysis, actionable reporting.
- OT Pentest
Operational Technology (OT) environments are the backbone of critical operations—but also prime targets for increasingly sophisticated threats. With DEFION’s OT Penetration Testing, leadership gains visibility into vulnerabilities that could disrupt production, safety, and continuity. Our approach uncovers risks in industrial systems, validates resilience against evolving threats, and delivers clear, prioritized insights to guide security investments where they matter most.
- OT Red Teaming
OT environments power production — but testing them is inherently risky if done without safeguards. DEFION’s OT Red Teaming delivers controlled, safety-first simulations of targeted attacks. Executives gain insight into real adversary tactics without jeopardizing uptime, equipment, or safety.

Turn 24/7 security monitoring into real response capability.
Speak with our experts and learn how rapid, expert-led response transforms your security posture.
Contact usContact us