
Red Team Engagement
How does your organization respond when a real adversary attacks?
✓ Scenario-driven — tailored to your actual threat profile
✓ People, processes, and technology tested under operational pressure
✓ OT Red Teaming possible for industrial environments
A pentest uncovers technical vulnerabilities. A Red Team Engagement simulates a real adversary — with a concrete goal, patience, creativity, and full freedom to exploit people, processes, and technology. It not only tests whether your preventive security measures work, but also whether your organization can truly detect, escalate, and respond.
That is a fundamentally different level of resilience testing.
The difference between a pentest and a Red Team Engagement
A pentest is a technical vulnerability analysis within a defined scope. Valuable — but it does not answer the question: "If a targeted attacker really wants to hit us, can we stop them?"
A Red Team Engagement does provide that answer. We simulate an Advanced Persistent Threat: a patient, targeted attack scenario where we are allowed to use all the tactics a real adversary would use.
What DEFION Red Teaming concretely delivers
Our Red Team specialists combine technical depth with operational realism:
✔ Threat profile-aligned scenario — Which attackers threaten your sector? What tactics do they use?
✔ Technical infiltration — Exploiting vulnerabilities in infrastructure, applications, cloud, and OT
✔ Social engineering — Targeted spear phishing, impersonation, pretext calls to your employees
✔ Physical or hybrid access — Where appropriate: badge cloning, tailgating, combined physical/digital attacks
✔ Persistence and lateral movement — We anchor ourselves and move through your environment like a real attacker
✔ Detection and response test — We measure how quickly and effectively your SOC, IT, and management respond
✔ No announcement — Your operational team does not know when it starts; we vary timing and tactics
✔ Technical and managerial debrief — Operational insights for your security team plus strategic summary for management
What type of Red Team suits your organization and needs?
Red Teaming is not a single service. The type depends on your sector, legal obligations, organizational maturity, and learning objectives. DEFION performs all the variants below.
Full Red Team Engagement
No announcement to the operational team. No limited scope. No hints. Our Red Teamers determine tactics, timing, and attack vector themselves — within the agreed rules of engagement. From initial reconnaissance and OSINT to social engineering, technical infiltration, lateral movement, and goal achievement. Your SOC does not know when it starts. Your CISO only finds out afterwards how far we got.
Suitable for: organizations with a mature and operational SOC that want to validate their detection capability under maximally realistic conditions.
Duration: 6–16 weeks depending on scope.
Bounded Red Team Engagement
Targeted attack simulation within a predetermined domain — external attack vectors, phishing and social engineering, cloud environment, or a specific supplier chain.
Useful when operational continuity does not allow full freedom, or when you want to thoroughly test one specific attack surface without burdening the rest of the organization.
Suitable for: organizations that want to address a blind spot purposefully, or that are not yet ready for an unbounded engagement.
Duration: 3–8 weeks.
Purple Team Engagement
Attack and defense in one combined exercise. Our Red Teamers execute techniques while your security team watches live, adjusts detection rules, and validates response procedures. Each technique is immediately translated into a detection gap or an improved SIEM rule.
Less realistic than an unbounded Red Team Engagement — but maximally educational.
OT Red Teaming
Attack simulation focused on industrial systems, SCADA, ICS, and operational technology — without risk to production continuity.
Most Red Team providers stop at the IT boundary. DEFION can fully include industrial environments in scope, including attack scenarios that exploit IT/OT convergence: from office network to production floor, from remote access to control logic. We know the specific threat actors targeting OT environments and the tactics they actually use.
Suitable for: manufacturing, energy, transport, water, critical infrastructure — any organization where a successful attack on OT systems endangers production, safety, or continuity.
Duration: 8–20 weeks depending on scope and OT complexity.
DNB Advanced Red Teaming (ART)
The DNB ART framework is an intelligence-led red team methodology for organizations under DNB supervision that are not yet ready for the full TIBER cycle. ART 2.0 is a structured intermediate step: heavier than a standard red team engagement, lighter in governance than TIBER.
An ART exercise follows a fixed phasing: preparation, threat intelligence, red team execution based on intelligence-led attack scenarios, and a mandatory purple team closure phase.
The ART framework is also used outside the financial sector — for hospitals and healthcare institutions under Z-CERT coordination (the so-called ZORRO framework) and for other critical infrastructure operators.
Suitable for: financial institutions and other organizations under DNB supervision that want to build their offensive test program towards TIBER or TLPT, and critical infrastructure sectors that want an ART-equivalent test.
Duration: 11–22 weeks.
TIBER-EU / TIBER-NL
The European framework for threat intelligence-based ethical red teaming of financial institutions, coordinated by the ECB and carried out in the Netherlands under DNB supervision. TIBER combines an independent Threat Intelligence Provider (TIP) with a Red Team Provider (RTP) in a controlled test of your production environment — including critical functions and critical third-party providers.
TIBER-NL was updated in February 2025 to fully align with the DORA TLPT standards. A successfully completed TIBER test can serve as TLPT evidence under DORA, provided it is conducted in accordance with the applicable RTS.
Suitable for: banks, payment institutions, pension funds, insurers, and other financial institutions under DNB or AFM supervision.
Duration: 9–14 months.
TLPT — DORA Article 26
Threat-Led Penetration Testing is a legal obligation as of January 17, 2025, for significant financial entities under DORA. The Regulatory Technical Standards come into effect on July 8, 2025 (EU 2025/1190). A full TLPT cycle every three years — or more often as directed by the competent authority.
DEFION guides you through the entire TLPT process: scope determination in coordination with the competent authority, coordination with the Threat Intelligence Provider, execution of the red team test on production systems, mandatory purple team closure, and delivery of the test report in accordance with RTS requirements.
Suitable for: financial institutions designated as significant under DORA (Article 26) — banks, payment institutions, investment firms, insurers.
Duration: 9–14 months.

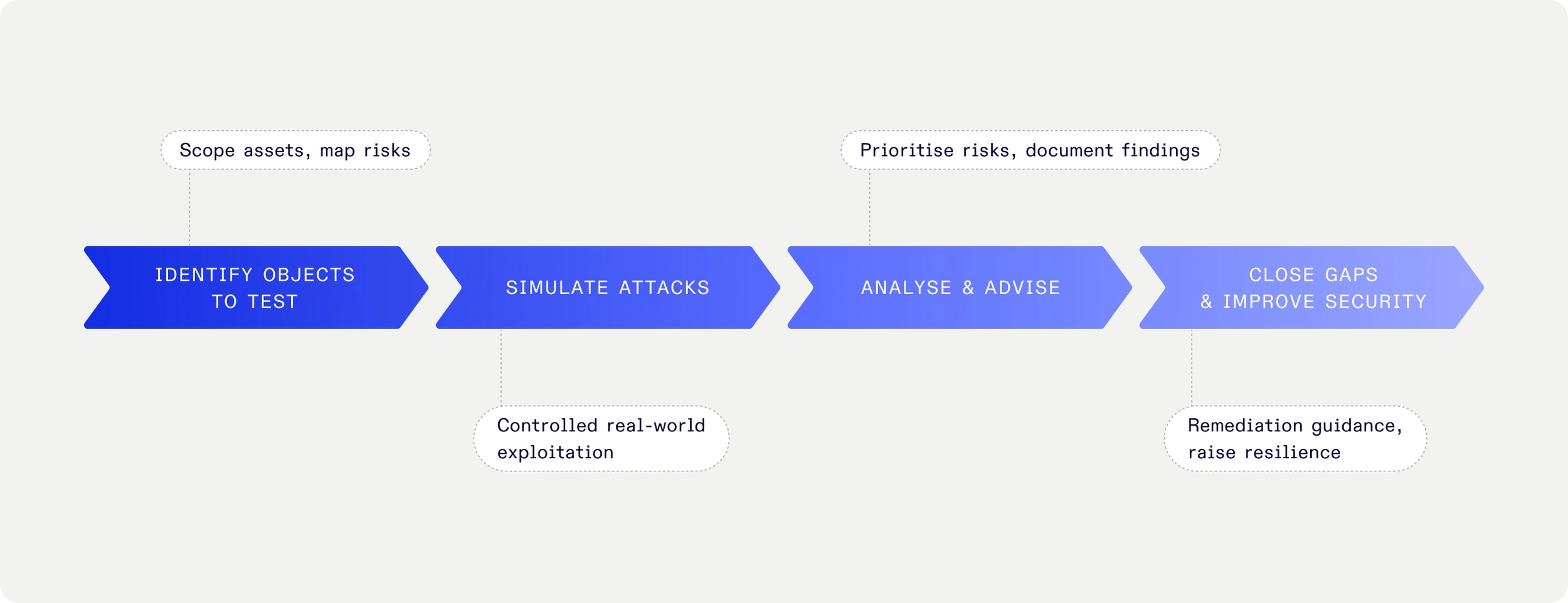
How a Red Team Engagement proceeds
1. Goal definition & scope
We determine together the scenario, objectives ("crown jewels"), scope, risk tolerance, and legal conditions. Who is allowed to know? Which systems are off-limits?
2. Threat modeling & attack planning
We analyze your sector, the current threat landscape, and OSINT about your organization. For intelligence-led engagements, the Threat Intelligence phase delivers specific attack scenarios based on your actual threat profile.
3. Execution
Our Red Team carries out the scenario. Your operational team does not know when it starts or what form it takes. We vary tactics and timing to maximize realism.
4. Monitoring & logging
All actions are recorded with exact timestamps, so during the debrief we can precisely reconstruct what was done, when it was detected (or not), and what the response was.
5. Debrief & improvement plan
- Technical debrief: Which techniques worked? Where were you stopped? What did your SOC miss?
- Purple team closure: Replay of attack techniques, live improvement of detection rules (mandatory for ART and TLPT)
- Executive summary: Strategic vulnerabilities and recommendations for management and CISO
Why DEFION?
OT expertise that most providers lack
Most Red Team providers stop at the IT boundary. We fully include OT environments, SCADA systems, and industrial networks in scope — with the knowledge and caution that this requires.
Connected with detection
Our Red Teamers also understand the detection side. They know which techniques modern EDR and SOC tooling recognize — and which they do not. This makes findings more actionable.
20 years of fieldwork as a foundation
DEFION conducts both red team operations and incident response. Our attackers also know what actually happens when a real attacker is in your environment — and what the damage is if detection fails.
One partner for the full spectrum
After a Red Team Engagement, you can turn to DEFION for pentesting, MDR, DFIR, and strategic advice. No handoff to another supplier.
For which organizations is Red Teaming suitable?
- Organizations with an existing and operational SOC that want to validate detection capability
- Sectors with increased threat levels: critical infrastructure, finance, government, manufacturing, OT
- Organizations legally required to perform an offensive test (TIBER, DORA TLPT, ART)
- Organizations where continuity and reputation depend on digital resilience
- OT environments where an attack on industrial systems endangers production or safety

"We were impressed by the openness and expertise of DEFION. The collaboration feels like alongside us, not against us - focused on the same goal." Client NIS2 and OT environment
"Thanks to DEFION, we benefit from up-to-date knowledge about contemporary security threats and means to avert risks. We have peace of mind knowing we are fully supported 24/7 by their team.”
Jeroen van Stokkum Manager ICT
![[object Object]](https://assets.defion.security/api/assets/images/l7GY2Z9ip58BiQ5Bckyaz6f4Kz3KdM-w2000.webp?t=3840)
“The sector and the partners we work with maintain increasingly high security standards for IoT-products and services. Protecting the privacy of individuals in the images and the sensitivity of the information the drones collect, such as on objects in critical infrastructure, requires our security to be airtight. With Defion, we are working with a professional partner who can support us at the right level. The collaboration also fits perfectly within our strategy to deliver reliable and secure drone technology to European customers.”
Benjamin van der Hilst Co-Founder & CEO

“New requirements from NIS2 for OT systems are increasing the focus on security. With Defion, we know we have the right expertise in-house to keep our systems secure. The collaboration was easy and pleasant; the specialists truly sat next to us rather than across from us. Thanks to their openness and expertise, we are working together toward the same goal: optimal security. This gives us the confidence to face the future.”
Alexander OdijkTeam Manager

“If you look at where we were ten years ago, we’ve made enormous progress. The sense of control is greater. With Security Assurance and MDR we have set up processes and control mechanisms that allow us to limit the impact of a potential attack. The collaboration also serves as a constant reminder to maintain focus on security and set the right priorities in that area. It keeps us alert and sharp. Moreover, Defion’s specialists are highly technical and passionate about their field. That clearly shows in their services.”
Gerco VermeerDevelopment Manager

Frequently Asked Questions
What is the difference between ART, TIBER, and TLPT?
TIBER-NL is the most comprehensive framework — a DNB-supervised test for financial institutions with an independent Threat Intelligence Provider. TLPT is the DORA requirement (Art. 26) that uses TIBER as the implementation standard. ART is a lighter, modular variant from DNB for organizations not yet ready for the full TIBER cycle — also deployable outside the financial sector, such as in healthcare (ZORRO framework, guided by Z-CERT).
Should we warn our operational team?
No — and preferably not. A general awareness ("a test will take place at some point") is acceptable. Timing or form is not; that undermines the scenario. Management and legal department are informed. Your SOC and operational team are not.
Can Red Teaming endanger our production environment?
We always discuss the specific risks and conditions in advance. For OT environments, we work with explicit safety protocols and escalation paths. Safety and production continuity come first.
How long does a Red Team Engagement last?
From 3 weeks (bounded) up to 14 months (TIBER/TLPT). See the comparison table. During the intake, we provide a concrete estimate based on your scope.
What if our team detects the Red Teamers?
That is the best scenario. We then increase the complexity and try other attack vectors. Detection is the goal — and the first step towards real resilience.
What does a Red Team Engagement cost?
This varies greatly based on scope, duration, and the chosen model. A scope discussion is free of charge. We provide a concrete indication within one business day.
Ready for a real resilience test?
Schedule a scope discussion with a Red Team specialist — we respond within one business day
- External Pentest
Your digital perimeter is the first thing adversaries will probe — and the first thing customers rely on. External Penetration Test simulates real-world attacks on your digital perimeter. Gain executive-level visibility of risks, validate defenses, and strengthen business continuity.
- Vendor Security Assessment
Assess and monitor the security maturity of your vendors with DEFION’s Vendor Security Assessment. Scalable, efficient, and board-ready for executive decision-making.
- Secure Development Training
DEFION’s Secure Development Training equips developers with secure coding skills to prevent vulnerabilities early in the lifecycle. Hands-on, standards-based, and tailored to your technology stack.
- Mobile App Security Assessment
Secure your iOS, Android, or cross-platform apps with DEFION’s Mobile App Security Assessment. Fast, collaborative, OWASP MASVS-aligned, and developer-focused.
- Email Risk Assessment
DEFION’s Email Risk Assessment evaluates and tests your organisation’s email security posture. Identify gaps, validate defenses, and receive actionable improvements against phishing, malware, and spoofing attacks.
- Cloud Security Assessment
With DEFION’s Cloud Security Assessment, leadership gains a clear understanding of how secure and resilient their cloud environments truly are. By assessing configurations, access controls, and exposure to evolving threats, DEFION highlights vulnerabilities that could impact business continuity and trust. Delivered with prioritized, executive-level insights, the service enables organizations to optimize cloud security investments, strengthen compliance, and maintain confidence in their digital transformation journey.
- Code Security Review
Identify vulnerabilities, logic flaws, and insecure implementations in your source code before they become risks. DEFION’s Code Security Review delivers expert manual analysis, clear reporting, and practical remediation advice to strengthen your application security.
- Internal Pentest
Cyber attackers don’t need to break the front door if they can move freely once inside. Our Internal Penetration Test gives executives a board-ready view of what an intruder could actually achieve within your environment — from accessing sensitive data to disrupting business operations.
- Web Application Pentest
With DEFION’s Web Application Penetration Testing, organizations gain clarity on the hidden risks within the digital services that drive customer engagement and business operations. By identifying vulnerabilities in web platforms before attackers can exploit them, DEFION helps leadership safeguard sensitive data, protect brand trust, and ensure business continuity. Delivered with clear, prioritized insights, our testing transforms complex technical findings into actionable guidance for executives—empowering smarter security decisions and stronger resilience.
- Red Teaming Services
DEFION Red Teaming delivers realistic cyberattack simulations to measure resilience and meet regulaatory requirements. Test detection, response, and business impact beyond penetration testing.
- Wireless Pentest
DEFION’s Wireless Penetration Test assesses WiFi security against real-world threats. Attack simulations, expert analysis, actionable reporting.
- OT Pentest
Operational Technology (OT) environments are the backbone of critical operations—but also prime targets for increasingly sophisticated threats. With DEFION’s OT Penetration Testing, leadership gains visibility into vulnerabilities that could disrupt production, safety, and continuity. Our approach uncovers risks in industrial systems, validates resilience against evolving threats, and delivers clear, prioritized insights to guide security investments where they matter most.
- OT Red Teaming
OT environments power production — but testing them is inherently risky if done without safeguards. DEFION’s OT Red Teaming delivers controlled, safety-first simulations of targeted attacks. Executives gain insight into real adversary tactics without jeopardizing uptime, equipment, or safety.

Turn 24/7 security monitoring into real response capability.
Speak with our experts and learn how rapid, expert-led response transforms your security posture.
Contact usContact us