OT Pentest
Operational Technology (OT) environments are the backbone of critical operations—but also prime targets for increasingly sophisticated threats. With DEFION’s OT Penetration Testing, leadership gains visibility into vulnerabilities that could disrupt production, safety, and continuity. Our approach uncovers risks in industrial systems, validates resilience against evolving threats, and delivers clear, prioritized insights to guide security investments where they matter most.
Operations Technology Pentesting
Operational Technology is at the heart of your business, but it was never designed to withstand today’s fast-changing cyber threats. As Industrial Control Systems connect to IT-networks, cloud applications and vendors, risks are on the increase. Targeted security testing helps to uncover vulnerabilities, strengthen your defence, and safeguard your operations in accordance with NIS2 and IEC-62443, in non disruptive manner.

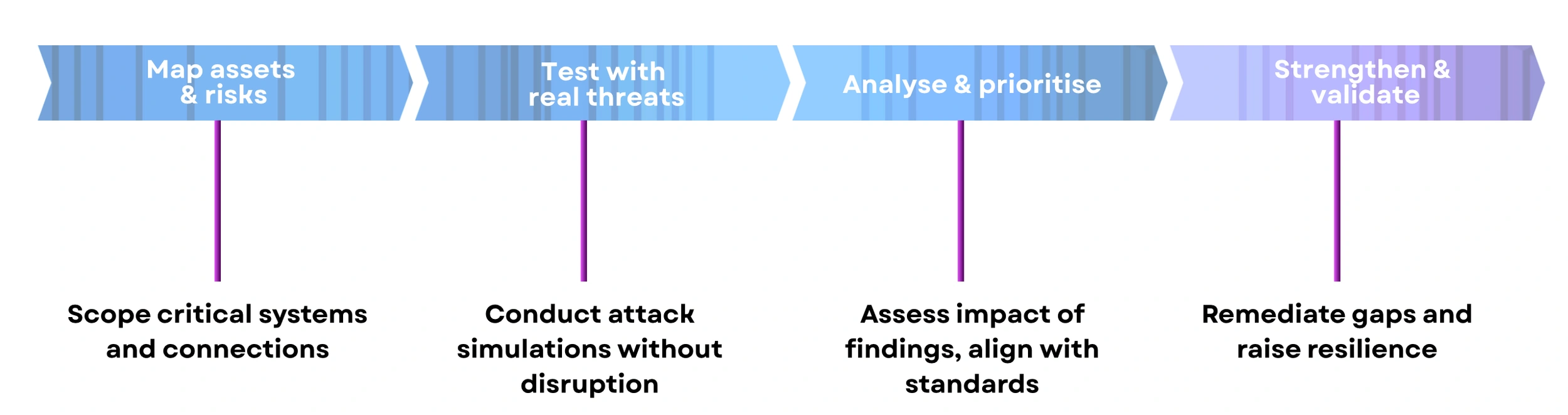
OT Pentesting Process
OT security testing process gives you full visibility of your operating technology environment and how it holds up against real-world threats. From mapping assets and simulating attacks to prioritising risks and validating improvements, to build lasting resilience without disrupting operations.
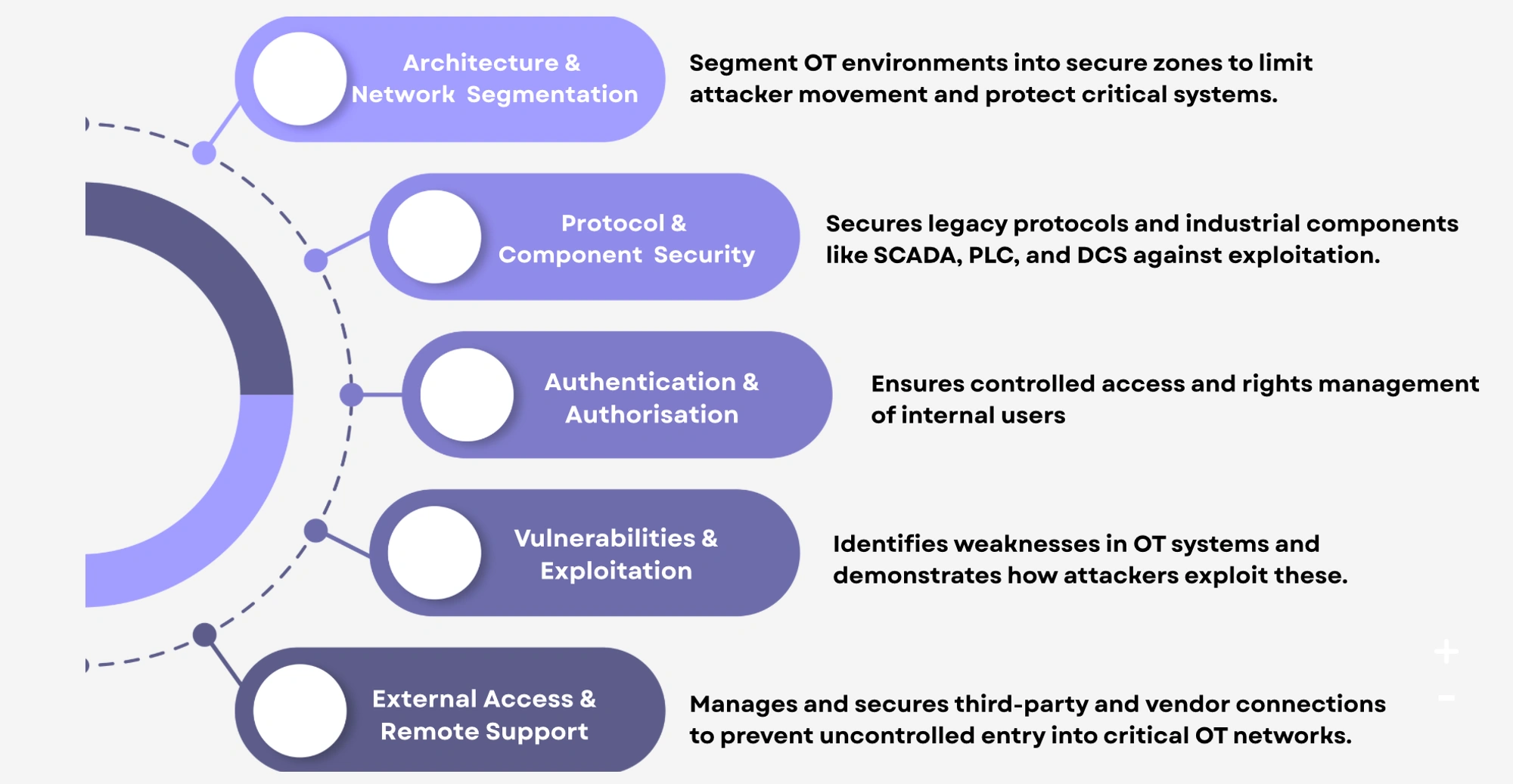
Our OT Pentesting Services include
Our OT security testing service examines every layer of your industrial environment to uncover real security gaps. This includes network segmentation and protocol security to user access, vulnerabilities, and external connections. Showing exactly where defences need strengthening to keep operations safe.
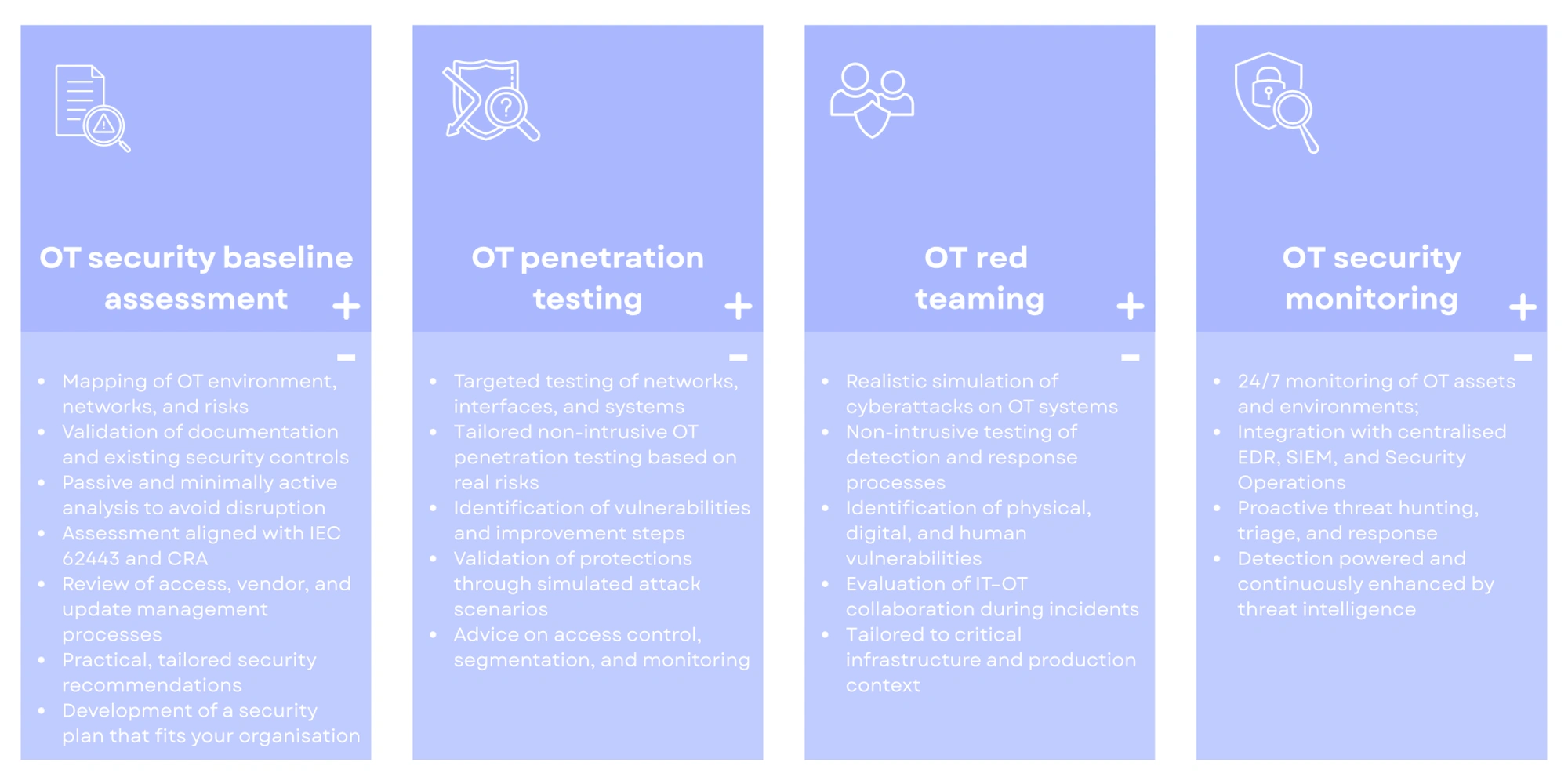
We offer 4 types of OT Security Services
Our four complementary OT security tests to match different needs and maturity levels. From a baseline assessment and targeted pentests to realistic red team simulations and continuous monitoring, each service strengthens resilience and protects critical operations.
What is Operational Technology Security?
Operational technology (OT) security is a specialized discipline dedicated to protecting the industrial systems that run critical processes and infrastructure. It focuses on environments such as SCADA, PLC, DCS, RTU, and IED platforms that control manufacturing, energy, utilities, and transport. Unlike IT networks, these systems often rely on outdated protocols and cannot tolerate downtime, making them uniquely vulnerable to modern cyber threats. OT Security addresses this reality through network segmentation, access control, protocol monitoring, and governance frameworks like IEC 62443. In addition, continuous monitoring, targeted penetration testing, and red teaming ensure that weaknesses are uncovered before attackers can exploit them. Every engagement is tailored to the operational environment, combining non-intrusive assessment methods with deep technical expertise to safeguard continuity and safety without disrupting production. Reports provide clear roadmaps to strengthen resilience and meet compliance obligations such as the Cyber Resilience Act.
Key advantages include:
- Protection of vital processes where downtime is not an option
- Actionable insights mapped to industry standards and regulatory frameworks
By combining industrial expertise with proven cybersecurity practices, OT Security gives organizations a clear and practical path to reduce risk, ensure safety, and maintain business continuity in the face of evolving cyber threats.
Why is OT Security essential in modern cybersecurity?
Modern OT environments are the backbone of industries such as energy, transport, and manufacturing. Yet they face growing risks from IT integration, remote access, and outdated technologies. Traditional IT security tools cannot safeguard these systems, as they overlook legacy protocols, operational constraints, and complex industrial architectures. Without targeted OT testing and monitoring, vulnerabilities remain hidden until they cause operational disruption or physical damage. OT security delivers hard evidence of how your industrial defences withstand real-world threats. It exposes the true impact of weaknesses, and provides a clear, prioritized roadmap to reduce risk, protect safety, and ensure uninterrupted operations.
- Protects critical processes where downtime is unacceptable
- Goes beyond IT tools to address legacy protocols and systems
- Identifies blind spots in IT–OT connections and remote vendor access
- Demonstrates resilience under realistic but non-disruptive industrial attack conditions
- Prioritises risks by real-world safety and continuity impact
- Provides clear, practical guidance to strengthen defences
Securing OT environments presents unique challenges that differ significantly from traditional IT security. These environments are often complex, outdated and cannot tolerate downtime. Patching options are limited and visibility into network architecture or remote access is often lacking.
Common challenges include:
-
No tolerance for downtime: Industrial environments commonly cannot experience any interruption. This makes it difficult to apply patches, updates, or other critical security measures.
-
Legacy systems and outdated protocols: Many OT environments run on technology never designed with modern security in mind. Patching is limited or impossible, leaving well-known vulnerabilities unaddressed.
-
Uncontrolled connections between IT and OT: Connections between IT and OT domains are often poorly documented or inadequately secured. These blind spots create opportunities for attackers to move laterally across IT and ultimately OT networks.
-
Risk-prone remote and third-party access: External vendors and maintenance teams frequently hold direct access to critical systems. This broadens the attack surface and complicates governance and accountability.
-
Lack of safe, realistic testing: Operators often fear ways to test their defences under real-world attack conditions because of the risk of business interruption. As a result, it remains uncertain whether systems can withstand current threats.

Turn 24/7 security monitoring into real response capability.
Speak with our experts and learn how rapid, expert-led response transforms your security posture.
Contact usContact us