Security Control Validation
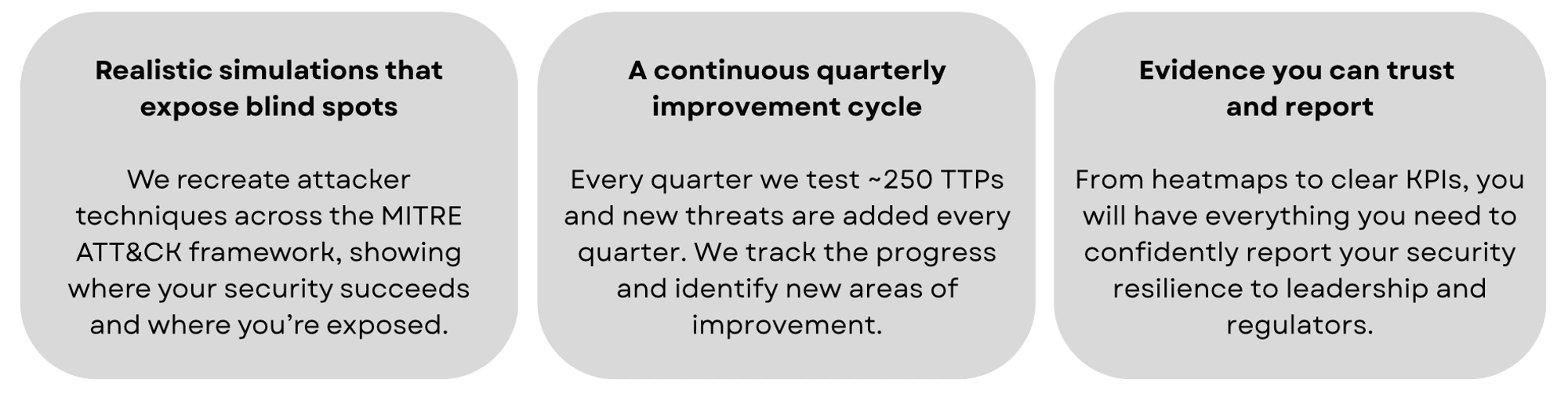
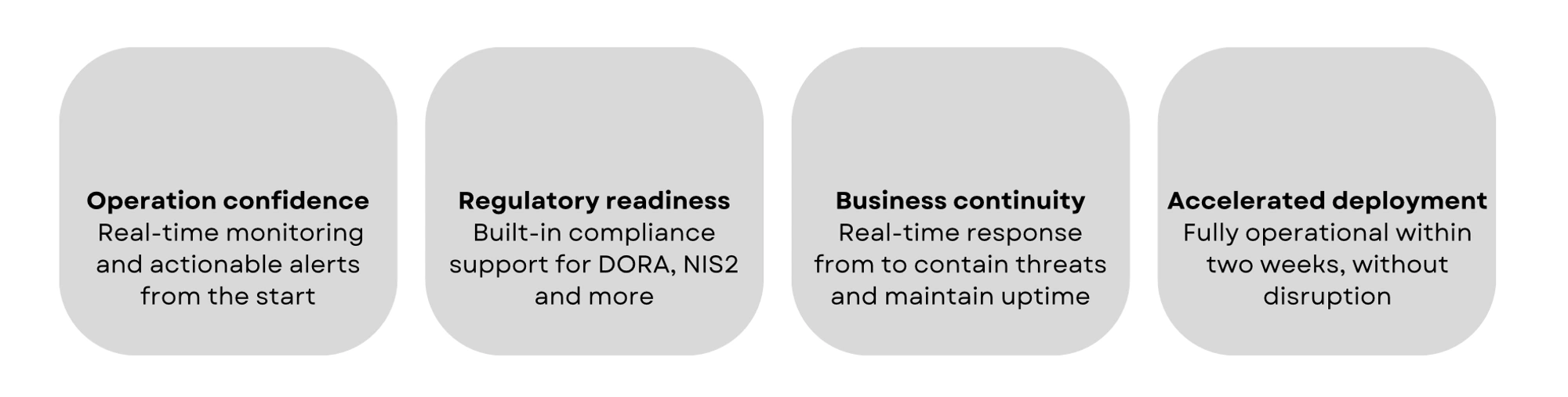
With DEFION’s Security Control Validation, leadership gains confidence that existing security investments deliver the protection they promise. By continuously testing, validating, and measuring the effectiveness of controls against real-world threats, DEFION provides executives with clear, prioritized insights into where defenses succeed and where gaps remain. This ongoing validation not only strengthens resilience and optimizes spending but also gives leadership assurance that business-critical operations remain protected under pressure.
We continuously test your security set up with the latest most advanced attacking methods so your security stays effective.

We simulate attacks following the MITRE ATT&CK® framework and identify where your system has identified them.
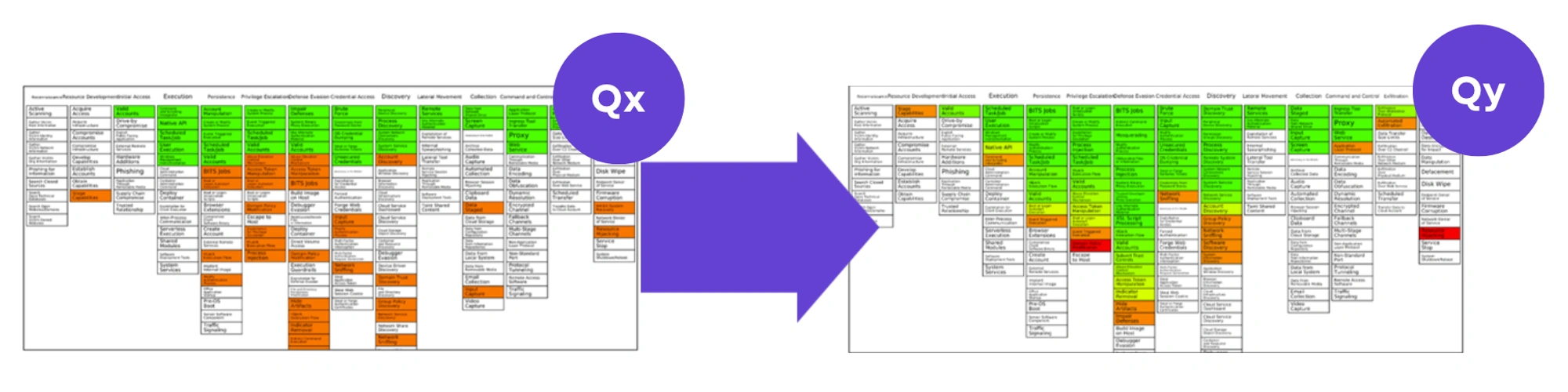
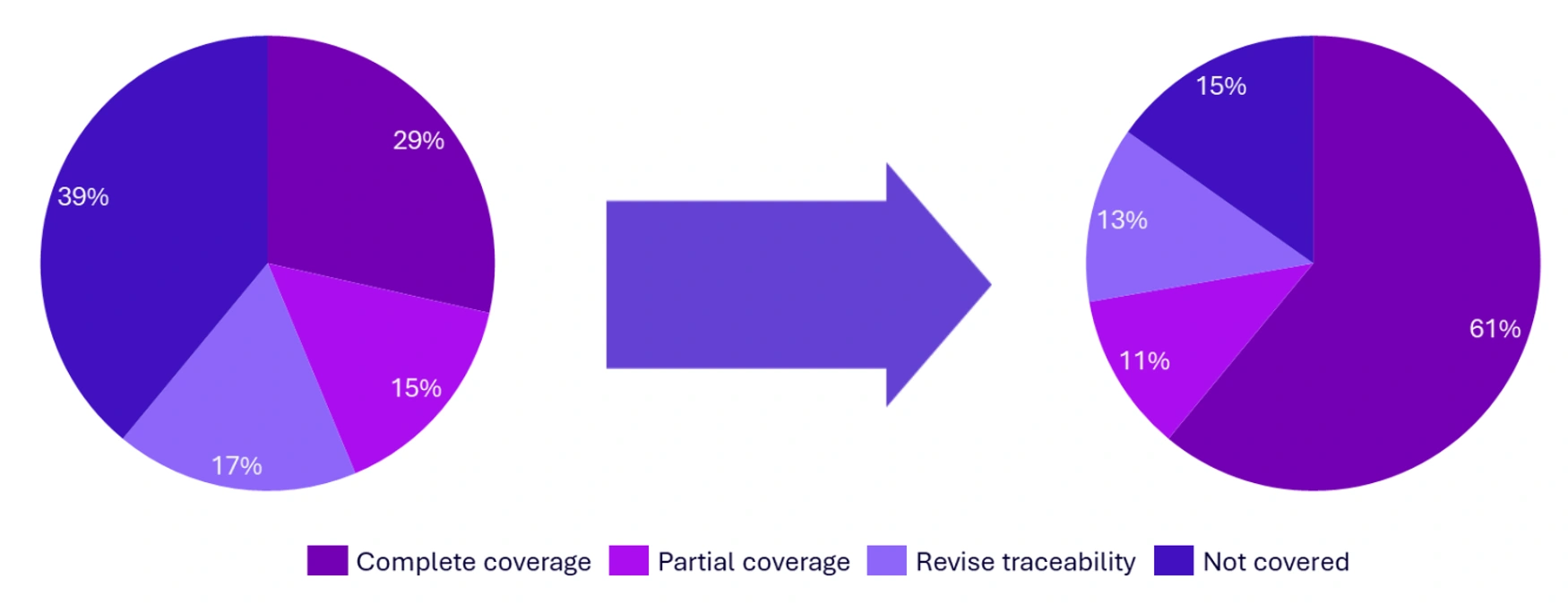
We create a heatmap based on the MITRE ATT&CK® framework to visually see the progress on your security level
Our breach & attack simulations deliver quarterly reports with KPIs, progress, and security improvement actions
What value will our Security Control Validation add?
What is Security Control Validation?
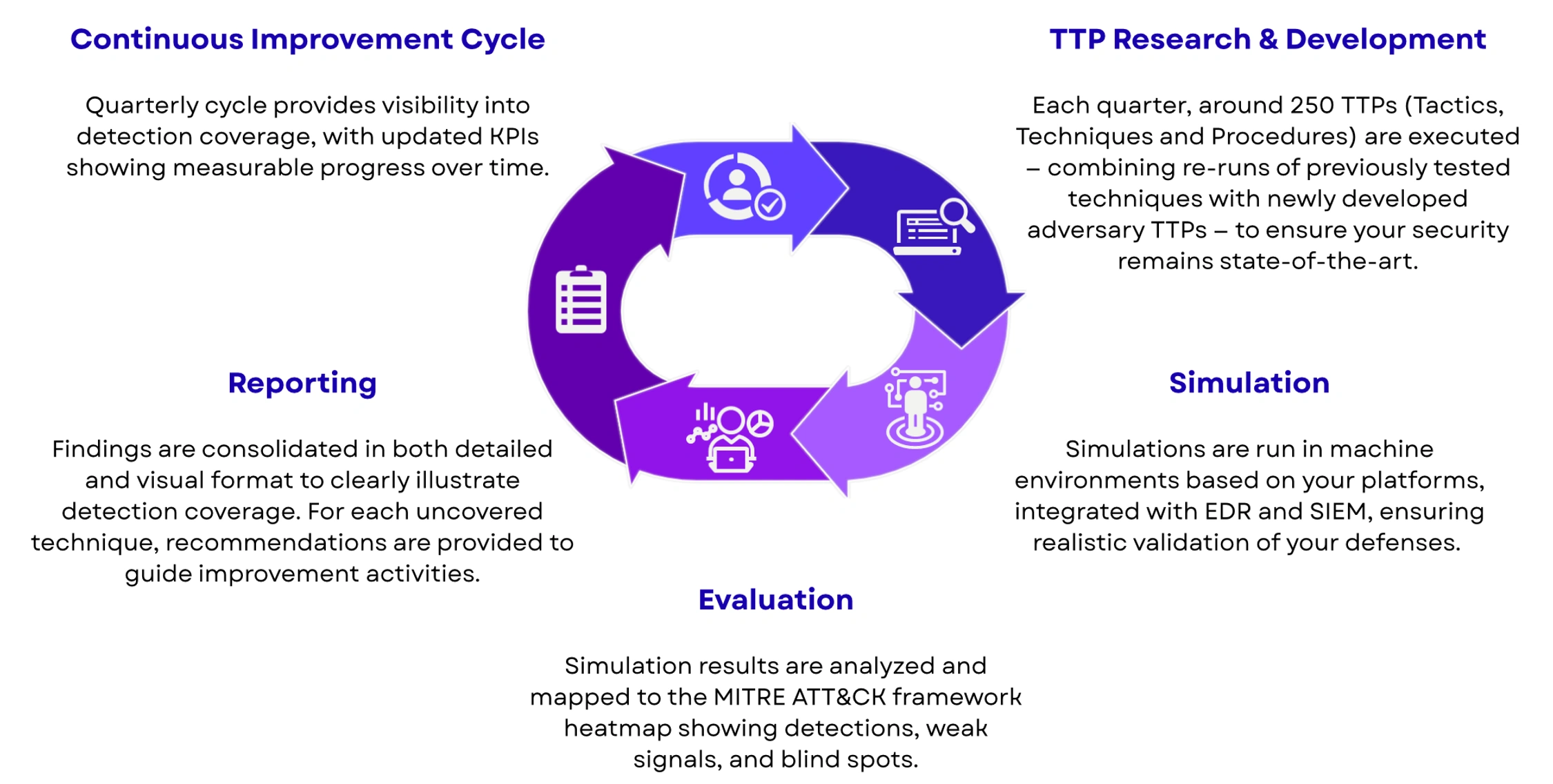
Security Control Validation (SCV) is a managed service that provides continuous proof of how well an organization’s defences detect and respond to cyberattacks. Using Breach and Attack Simulation (BAS) technology, it runs realistic attack scenarios aligned with MITRE ATT&CK, fully integrated into the client’s SIEM and EDR tools. This approach delivers a clear, evidence-based view of detection performance, showing not just whether alerts trigger, but how effective the overall response process is. Unlike point-in-time tests, SCV establishes an ongoing cycle of testing, tuning, and improving detection capabilities. Each quarter, new attack techniques are introduced, existing scenarios re-validated, and results visualized through KPIs, heatmaps, and dashboards. With expert Red and Blue Team input, SCV turns detection into a measurable, continuously improving capability.
Key advantages include:
- Continuous BAS-driven simulations that replicate evolving adversary tactics and techniques
- KPIs, metrics, and heatmaps that visualize detection coverage and progress over time
- Expert guidance from Red and Blue Teams to refine detection rules and mitigation strategies
What are the main challenges in your security?
-
Many organizations struggle to understand whether their detection systems actually perform against real-world attack techniques rather than theoretical threats.
-
Traditional audits and one-time penetration tests provide only static snapshots that fail to capture evolving infrastructures and dynamic adversary behaviour.
-
There is often no reliable evidence or KPIs to validate detection coverage or justify investments in monitoring technologies.
-
Misalignment between SOC analysts, red teams, and blue teams can create gaps in tuning, validation, and response coordination.
-
Security leaders lack clear, visual reporting such as heatmaps or coverage metrics to confidently demonstrate detection maturity to executives and regulators.
-
Static playbooks and alert rules are rarely updated at the pace of modern adversaries, leaving blind spots that monitoring alone cannot close.
Why DEFION?

Turn 24/7 security monitoring into real response capability.
Speak with our experts and learn how rapid, expert-led response transforms your security posture.
Contact usContact us