
Attackers work 24/7. The security specialists in our SOC do too.
✓ 24/7 SOC monitoring - also outside office hours and on weekends
✓ IT and OT monitoring under one roof - no blind spots
✓ Vendor-neutral - we connect to your tooling
Attackers work 24/7. The average time between breach and detection is 194 days — more than six months during which an attacker is active unnoticed in your environment.
DEFION MDR structurally reduces that window: continuous monitoring, advanced detection, and immediate response by experienced SOC analysts, day and night. Vendor-neutral and tailored to your digital environment - whether it concerns IT, OT, or other assets.
What goes wrong without MDR?
MDR acts as your fire alarm system, control room, and emergency service for cyber incidents. Without MDR, you miss opportunities to detect and stop attacks early - before damage is done.
Many organizations have solutions like EDR, firewalls, and SIEM. Yet attacks are missed. Not because the tools fail, but because no one interprets and follows up on the signals 24/7.
What is missing without active MDR:
• Continuous analysis of security events outside office hours
• Quick interpretation of suspicious patterns in context
• Immediate follow-up on incidents — not after hours or days
• Capacity to correlate threats across systems
Attackers move slowly and deliberately. Every day detection is delayed increases the damage, recovery time, and legal exposure.
What DEFION MDR concretely offers you
No black box. No anonymous ticket system. But a direct line with specialists who know your environment.
✔ 24/7 monitoring of critical systems, endpoints, and network
✔ Advanced detection rules - no generic signatures, but context-driven analysis
✔ Fast triage and validation - we filter noise, you only get what matters
✔ Direct containment and response - we act, or guide your team in acting
✔ IT and OT coverage - we monitor industrial environments where other MDR providers drop out
✔ Threat Intelligence - current threat information integrated into our detection mechanisms
✔ Clear reporting - periodic evaluation with concrete insights
✔ Vendor-neutral - we work with your existing tools, no mandatory products
What we monitor
Endpoint Detection & Response (EDR)
Monitoring and protection of all your digital assets: workstations, laptops, servers, etc. Detection of suspicious behavior in your environment(s) — including malware, lateral movement, and privilege escalation.
Log and SIEM Integration
Central correlation of log data from your entire environment. We integrate with your existing SIEM or provide our own infrastructure. This way, we monitor your entire attack surface.
Network Detection & Response (NDR)
Analysis of network traffic for anomalies, unauthorized connections, and C2 communication. Detection of movements that endpoint tools miss.
Threat Intelligence
Continuous integration of current threat information - including dark web monitoring for leaked credentials and indicators specifically relevant to your sector and organization type.
OT Security Monitoring
Specific monitoring of industrial environments and OT networks. We understand the operational constraints of OT and adapt our approach - without impacting the continuity of your processes. No agents on production PLCs, we fully tailor the approach to your architecture.
Incident Response Support
In the event of an incident, our incident handlers and investigators are ready immediately. From initial triage to forensic investigation and recovery - all under one roof.

Why DEFION — and not another MDR provider?
IT and OT in one service
Most MDR providers monitor IT environments. DEFION also monitors industrial OT networks — with knowledge of OT protocols, safety-critical systems, and the specific threats to manufacturing, energy, and transport.
Born from twenty years of fieldwork
DEFION originated from Computest Security and Incide — two cybersecurity specialists with decades of experience in penetration testing, incident response, and strategic advice. Our SOC analysts have personally uncovered vulnerabilities and responded to incidents. That makes the difference in recognition.
Vendor-neutral and without lock-in
We do not sell products. We integrate with what you already have. No mandatory tool purchase, no vendor extension as an upsell.
DFIR under one roof
If it escalates to a serious incident, our Digital Forensics & Incident Response specialists are ready immediately. No external escalation path — one partner for detection and response.
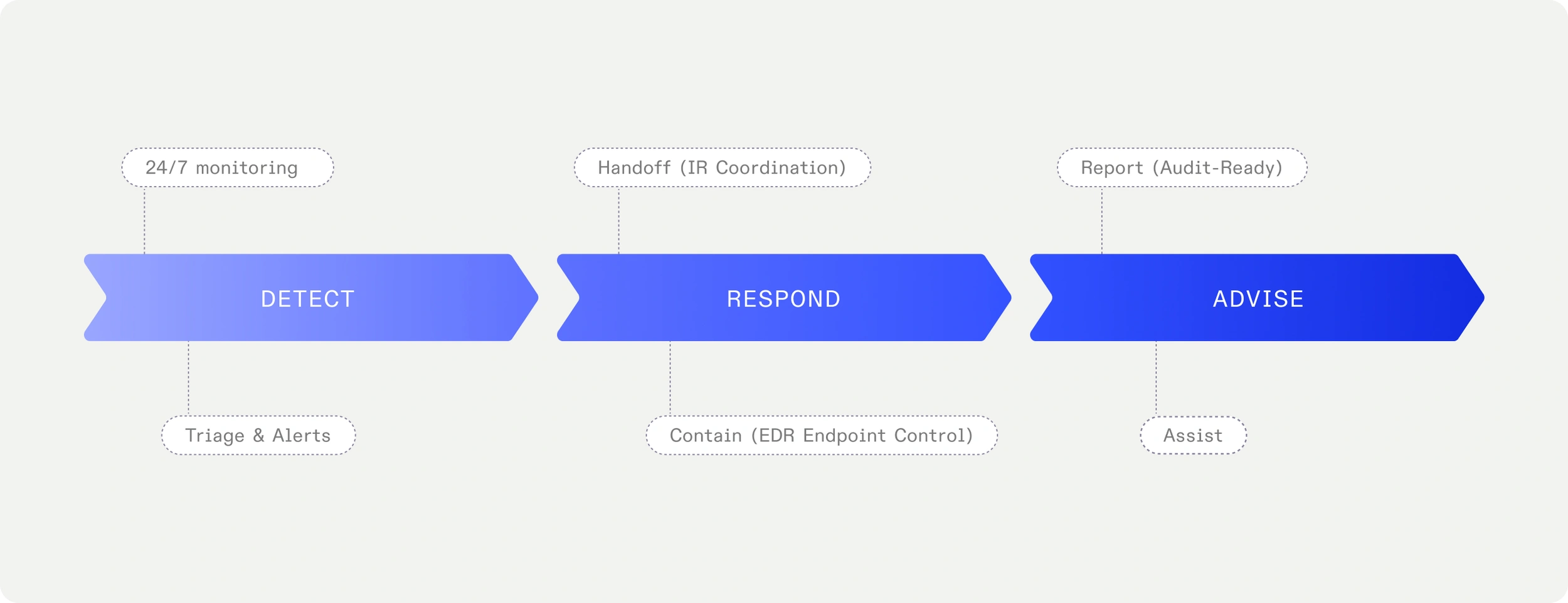
How an MDR process works
-
Intake & scope definition
We map your environment, risk profile, and monitoring objectives. No standard package — scope tailored to your sector, size, and OT components. -
Implementation & onboarding
We configure integrations, detection rules, and response procedures. Your team doesn't need to be an MDR expert — we guide every step. -
Continuous monitoring
Our SOC analysts monitor and analyze 24/7. When an alert requires action, we act immediately or involve your team via the agreed escalation procedure. -
Reporting & optimization
Periodic evaluation of detection rules, threat landscape, and your security maturity. We get to know your environment better and become increasingly effective at detecting anomalies.
For organizations that prefer to outpace attackers
DEFION MDR is the right answer for organizations:
- With business-critical digital or industrial processes where downtime is unacceptable
- In regulated sectors: critical infrastructure, finance, government, healthcare, industry
- With limited internal SOC capacity but still needing 24/7 visibility
- That must demonstrate to NIS2, DORA, or insurers that they actively monitor and can respond
- That want to structurally improve after an incident and prevent recurrence
- With OT environments overlooked by other providers

"Thanks to DEFION, we benefit from up-to-date knowledge about contemporary security threats and ways to prevent risks. We have peace of mind knowing that we are fully supported by their team 24/7." AFAS Software
"Thanks to DEFION, we benefit from up-to-date knowledge about contemporary security threats and means to avert risks. We have peace of mind knowing we are fully supported 24/7 by their team.”
Jeroen van Stokkum Manager ICT
![[object Object]](https://assets.defion.security/api/assets/images/l7GY2Z9ip58BiQ5Bckyaz6f4Kz3KdM-w2000.webp?t=3840)
“The sector and the partners we work with maintain increasingly high security standards for IoT-products and services. Protecting the privacy of individuals in the images and the sensitivity of the information the drones collect, such as on objects in critical infrastructure, requires our security to be airtight. With Defion, we are working with a professional partner who can support us at the right level. The collaboration also fits perfectly within our strategy to deliver reliable and secure drone technology to European customers.”
Benjamin van der Hilst Co-Founder & CEO

“New requirements from NIS2 for OT systems are increasing the focus on security. With Defion, we know we have the right expertise in-house to keep our systems secure. The collaboration was easy and pleasant; the specialists truly sat next to us rather than across from us. Thanks to their openness and expertise, we are working together toward the same goal: optimal security. This gives us the confidence to face the future.”
Alexander OdijkTeam Manager

“If you look at where we were ten years ago, we’ve made enormous progress. The sense of control is greater. With Security Assurance and MDR we have set up processes and control mechanisms that allow us to limit the impact of a potential attack. The collaboration also serves as a constant reminder to maintain focus on security and set the right priorities in that area. It keeps us alert and sharp. Moreover, Defion’s specialists are highly technical and passionate about their field. That clearly shows in their services.”
Gerco VermeerDevelopment Manager

Frequently Asked Questions
What is the difference between MDR and a regular SIEM or SOC?
A SIEM collects and correlates data — but does not respond itself. An internal SOC requires its own staff, knowledge, and coverage. MDR combines technology, threat intelligence, and experienced analysts who work for you 24/7, without you having to build or staff a team yourself.
Does DEFION MDR work with our existing tooling?
Yes. We are vendor-neutral and integrate with your existing EDR, SIEM, and other security tools. No mandatory products, no lock-in. If your tooling falls short, we advise on this — but we do not decide for you.
Does DEFION MDR also cover OT environments?
Yes — this is one of our strongest differentiators. We monitor both IT and OT, with specific knowledge of industrial protocols and the operational constraints of OT environments. No disruption of production processes.
How quickly does DEFION respond to an incident?
For critical incidents, we act immediately — containment, isolation, and escalation without delay. The exact response procedure and escalation structure are established during the intake, tailored to your context.
Does DEFION MDR comply with NIS2 and DORA requirements?
Yes. Active monitoring and demonstrable detection and response capabilities are explicit requirements under NIS2 and DORA. DEFION MDR provides the documentation, logging, and reporting you need for compliance and audits.
What if we already have a SIEM — is MDR still necessary?
A SIEM without staffing is an instrument without a musician. MDR adds the human expertise, 24/7 presence, and active response that a SIEM tool itself cannot provide.
What does MDR cost at DEFION?
Costs depend on scope, size, and desired integration levels. Contact us for a tailored indication — we respond within one business day.
Do you want continuous control over your security risks?
Schedule an intake interview with an MDR specialist - we respond within one business day
- Imminent Threat Exposure
Cyber adversaries are constantly probing for weaknesses — often before organizations even realize they are a target. With our Imminent Threat Exposure service, you gain real-time visibility into active threats, adversary intent, and emerging risks specific to your business. By anticipating attacks instead of merely reacting, you strengthen decision-making, reduce uncertainty, and protect critical operations with foresight.
- Managed Threat Detection
Attackers don’t wait — and neither should your defenses. Our Managed Threat Detection service provides 24/7 monitoring, advanced analytics, and expert validation to uncover malicious activity before it escalates. By detecting threats early and distinguishing real risks from noise, we help your organization reduce dwell time, limit impact, and safeguard continuity.
- Managed Threat Hunting
Cyber threats often lurk undetected, bypassing automated defenses and waiting to cause damage. Our Managed Threat Hunting service takes a proactive approach: expert analysts actively search for hidden adversaries across your environment, validating suspicious activity before it escalates. This continuous hunt not only reduces dwell time but also strengthens your cyber defense, ensuring your organization stays one step ahead of attackers.
- Managed Extended Detection & Response (MXDR)
With DEFION’s Managed Detection & Response (MDR), your organization benefits from continuous, 24/7 monitoring and response designed to stop threats before they disrupt operations. Rooted in our Active Defense approach, MDR combines advanced detection, expert analysis, and immediate action to neutralize risks in real time. For executives, this means peace of mind: knowing that business continuity, reputation, and resilience are safeguarded around the clock by a trusted security partner.
- Security Control Validation
With DEFION’s Security Control Validation, leadership gains confidence that existing security investments deliver the protection they promise. By continuously testing, validating, and measuring the effectiveness of controls against real-world threats, DEFION provides executives with clear, prioritized insights into where defenses succeed and where gaps remain. This ongoing validation not only strengthens resilience and optimizes spending but also gives leadership assurance that business-critical operations remain protected under pressure.
- Continuous Vulnerability Management
Cyber risk isn’t static — new vulnerabilities emerge daily, and attackers move fast to exploit them. Our Continuous Vulnerability Management service provides an always-on view of your security posture, prioritizing the risks that matter most to your business. With expert validation and remediation guidance, you gain control over exposure, reduce attack surfaces, and ensure resilience without drowning in alerts.
- Managed Threat Intelligence
Threat intelligence is only valuable if it drives action. With our Managed Threat Intelligence service, you gain curated, context-rich insights aligned to your industry, assets, and threat landscape. We cut through the noise to deliver what’s relevant — enabling informed strategic decisions, optimized defenses, and resilience against adversaries that evolve daily.
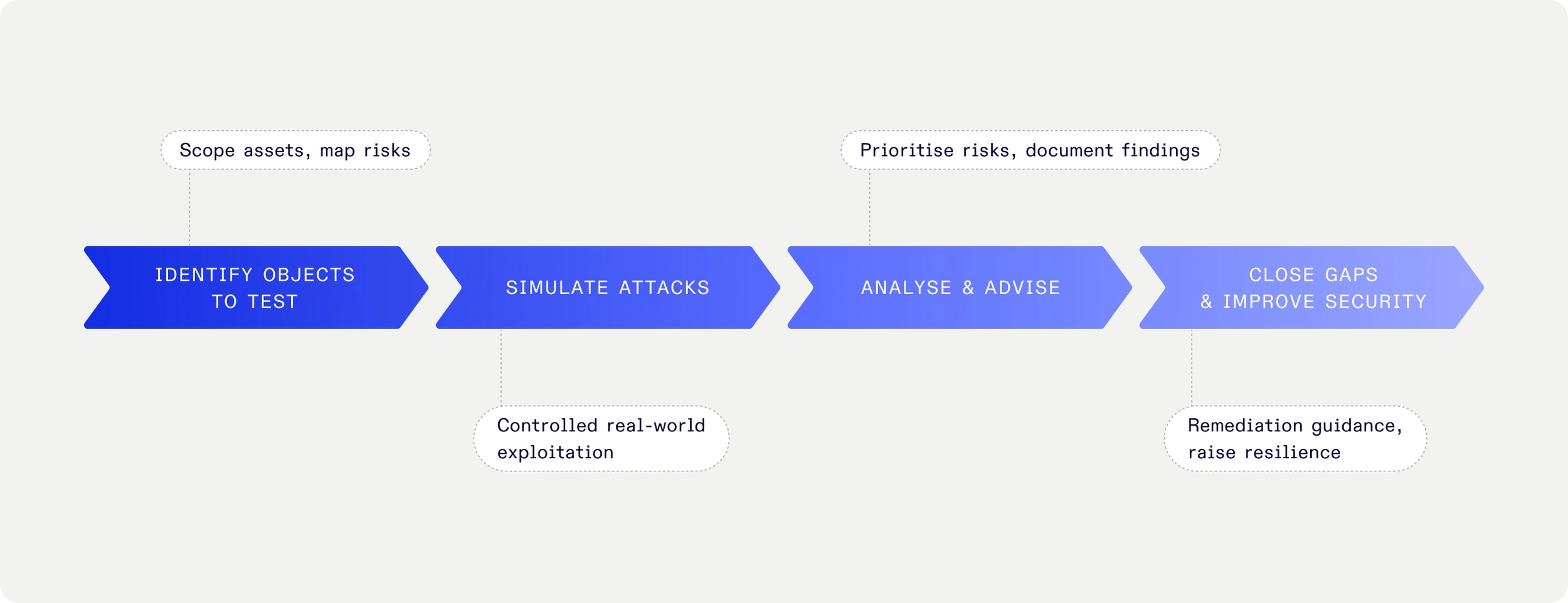
- Purple Teaming
Strong cyber defense isn’t built on assumptions — it must be tested. Purple Teaming combines controlled attack simulations with collaborative validation to measure and improve your organization’s defensive capabilities. By exposing weaknesses, validating detection, and sharpening response, we deliver actionable improvements that strengthen resilience and prove the effectiveness of your security investments.
- OT Security Monitoring
OT environments are too valuable — and too vulnerable — to leave unmonitored. DEFION’s OT Monitoring provides 24/7 detection, response, and threat hunting across industrial systems. With deep integration into IT and OT landscapes, your organization gains real-time visibility and expert response when every second counts.

Turn 24/7 security monitoring into real response capability.
Speak with our experts and learn how rapid, expert-led response transforms your security posture.
Contact usContact us