Incident Response Services
Incident Response is how you regain control when a cyberattack hits. When it does, it’s not just your IT but your operations, customers, and reputation are at stake. DEFION helps you take control fast: contain the threat, investigate what happened, and recover critical systems. We guide you through every step.The goal: reduce impact now, and build stronger resilience for what comes next.
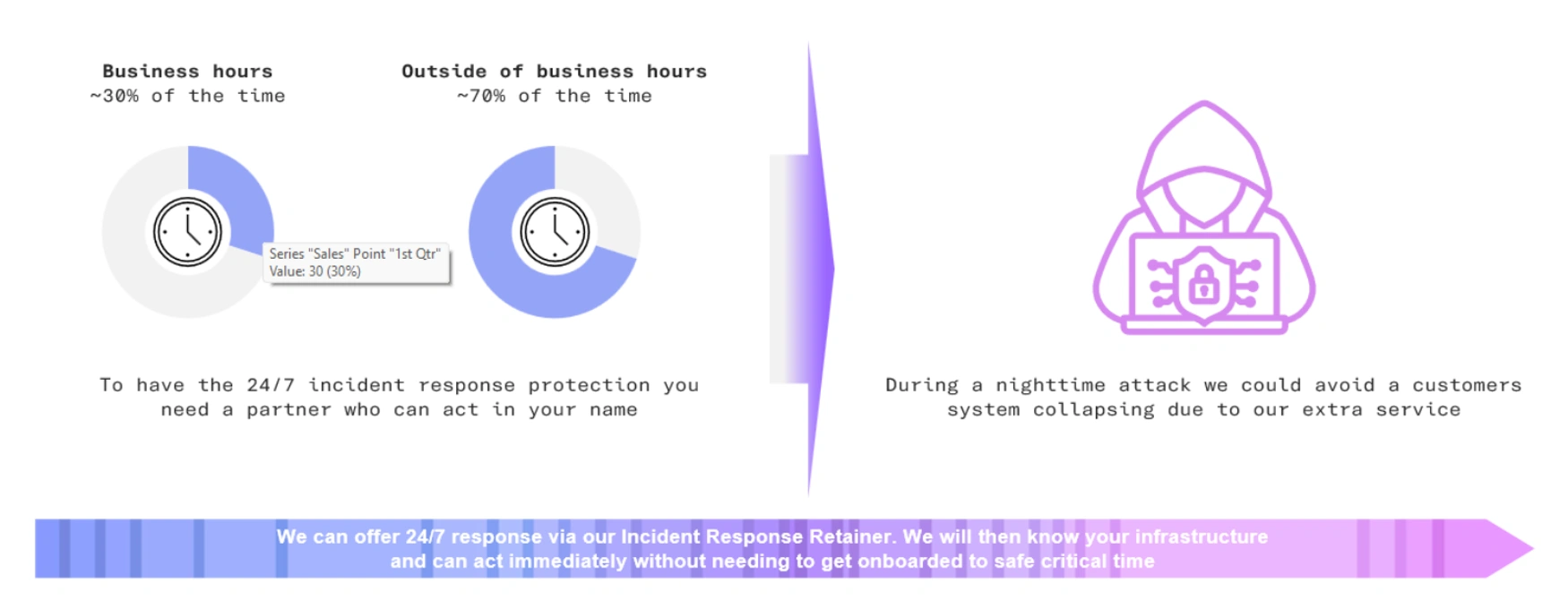
You are protected around the clock
If an incident occurs, our knowledge of your infrastructure enables faster response, containment, and reduced impact.
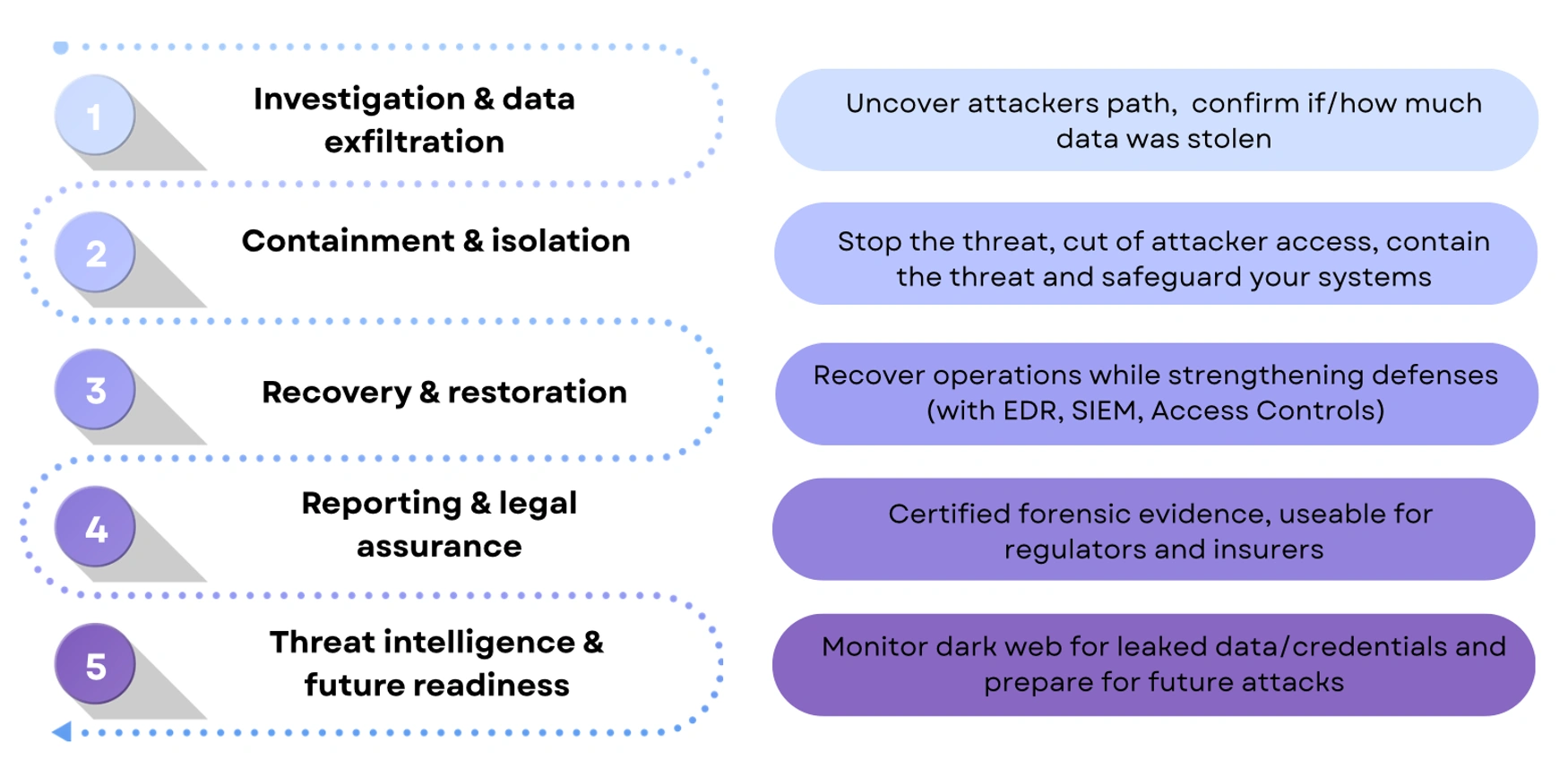
Our Incident Response Services
In case of an incident, we will follow a structured process to identify, contain, recover and report. We will uncover attackers path, stop the threat by cutting the attacker's access to safeguard your system and recover the system. On top, we deliver certified forensic evidence and advice on future readiness.
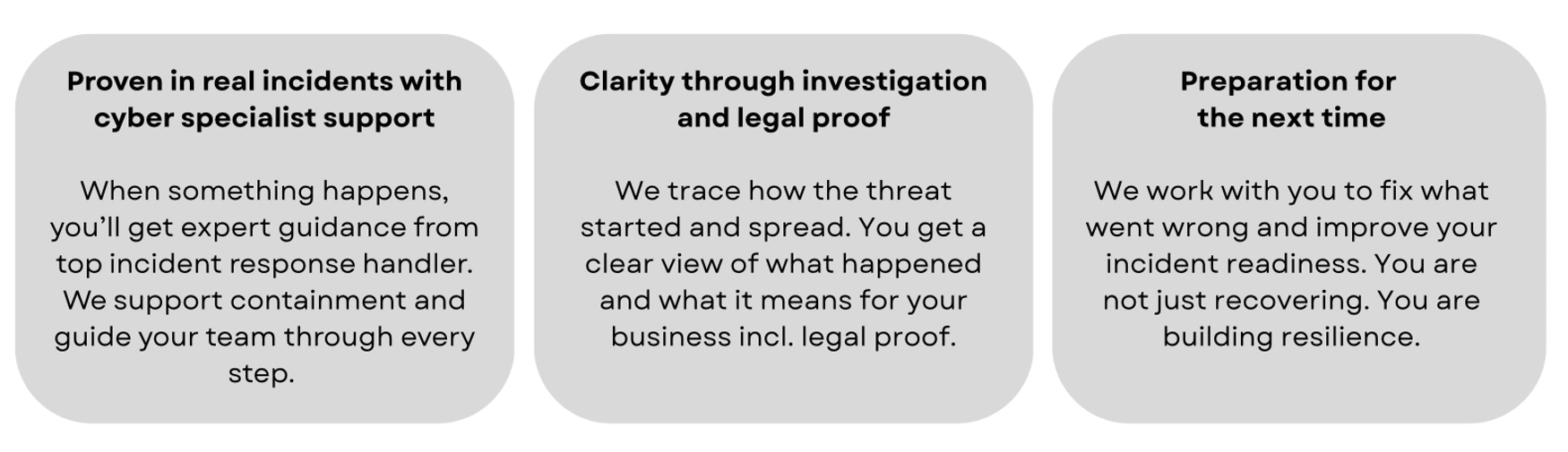
Value of our incident response services
Why is Incident Response essential in modern Cybersecurity?
Modern cyberattacks move fast. Ransomware can encrypt entire environments within minutes, data theft can go undetected for weeks, and targeted attackers exploit small gaps to cause large-scale disruption. Without a tested response capability, downtime increases, costs spiral, and trust erodes. Incident Response ensures that threats are contained before they spread, evidence is preserved for investigations, and operations are restored quickly and safely.
DEFION’s Incident Response helps organizations stay resilient in the face of evolving threats. Faster containment reduces the impact of breaches, forensic analysis provides the evidence required for compliance and legal proceedings, and expert-led recovery restores confidence both internally and externally.
-
Rapid Containment- Cyberattacks such as ransomware can spread within minutes. Swift isolation prevents escalation and limits disruption to business-critical operations.
-
Forensic Evidence - Incidents leave behind traces that are vital for compliance and legal defence. Proper evidence collection ensures accurate investigations and supports regulatory reporting.
-
Clear Coordination - During a crisis, uncertainty slows response. Defined playbooks and expert guidance provide clarity, reduce confusion, and keep teams aligned.
-
Structured Recovery - Downtime directly impacts revenue and reputation. Incident Response ensures fast, safe restoration of systems and processes to minimize financial loss.
-
Future Resilience - Every incident is also a learning opportunity. Post-incident advisory strengthens processes, improves monitoring, and reduces the likelihood of repeat attacks.
What is Incident Response?
Incident Response (IR) is a critical cybersecurity capability designed to stop active threats, minimize damage, and restore business operations quickly. It combines rapid containment, digital forensics, and coordinated recovery led by our expert incident response handlers responders who operate in real-world crises daily. Unlike preventive security tools that focus on detection, Incident Response provides hands-on support during an active attack, ensuring every minute is used effectively to reduce impact. With predefined playbooks, forensic readiness, and 24/7 availability, IR enables organizations to act decisively, preserve evidence, and recover with confidence. Engagement models range from immediate crisis response to retainer-based services, ensuring faster access to expertise when it matters most.
Key advantages include:
- Immediate containment to prevent ransomware, malware, or intrusions from spreading across systems and networks.
- Forensic analysis to identify entry points, attacker behaviour, and compliance-relevant evidence.
This combination of speed, deep expertise, and structured recovery ensures that organizations not only limit the impact of today’s incidents but also strengthen their resilience against the threats of tomorrow.
How Incident Response work in practice
Incident Response is a comprehensive process that enables organizations to act with speed, clarity, and confidence when faced with a cyberattack. It begins with coordination, ensuring that roles, responsibilities, and communication channels are established immediately so the response remains organized even under pressure. From there, expert investigators work to uncover how the incident started, which systems were affected, and what risks remain active across the environment. Containment and isolation limit the spread of ransomware, malware, or intruder activity while preserving critical evidence that is essential for forensic investigation and regulatory compliance. Recovery and restoration then focus on safely returning business operations to normal, reducing downtime, mitigating financial losses, and rebuilding trust. Finally, reporting and readiness transform the lessons of the incident into actionable improvements that strengthen processes, guide compliance obligations, and build resilience for the future. By combining technical expertise, forensic discipline, and structured recovery, incident response has become one of the most vital components of modern cybersecurity, ensuring that organizations can withstand attacks and emerge stronger.

Turn 24/7 security monitoring into real response capability.
Speak with our experts and learn how rapid, expert-led response transforms your security posture.
Contact usContact us