
DDoS Testing
DDoS Testing
Your DDoS protection is only as strong as the last time you tested it.
✓ Controlled simulations of volumetric, protocol, and application attacks
✓ Validation of mitigation, CDN, scrubbing, and internal response procedures
✓ Concrete improvement recommendations — not just measuring, but also improving
DDoS attacks are no longer the domain of activists with a download tool. Modern attacks are orchestrated, multi-vector, and targeted at specific vulnerabilities in your defense. The question is not if your organization will be targeted — but whether your defense will hold when it happens.
A DDoS test gives you that answer, before an attacker does.
Why test DDoS protection — and not just purchase it?
Organizations invest in DDoS mitigation: scrubbing services, CDN configurations, rate limiting, fail-over architecture. But how do you know that all these layers are correctly configured and work together under real attack pressure?
What remains untested is uncertain:
- Whether your CDN and scrubbing provider can handle the attack volumes that truly threaten you
- Whether your firewall rules fail or hold up during a SYN flood
- Whether your fail-over procedures are executed timely and correctly
- Whether your team detects attacks in time and follows the correct escalation steps
- Whether your application layer is resistant to slowloris and HTTP flood attacks
- Whether your critical API endpoints are specifically vulnerable to targeted application layer attacks
Mitigation software that has never been put under pressure offers paper security. A controlled DDoS test provides demonstrable assurance.

What DEFION DDoS Testing concretely delivers
Our specialists simulate realistic attack scenarios tailored to your threat profile and architecture:
✔ Volumetric attacks — UDP floods, ICMP storms, DNS amplification: test whether your bandwidth and scrubbing capacity hold up
✔ Protocol-oriented attacks — TCP SYN floods, fragmented packet attacks, ACK floods: validation of stateful inspection and firewall behavior
✔ Application layer attacks (Layer 7) — HTTP/HTTPS floods, slowloris, cache-busting: test of WAF, rate limiting and backend capacity
✔ Multi-vector attacks — Combined attack types simultaneously, as a real targeted DDoS attack works
✔ Mitigation validation — Confirmation that your CDN, scrubbing and anti-DDoS services respond correctly
✔ Detection and response test — Measurement of time-to-detect and time-to-respond by your team and procedures
✔ Impact and degradation analysis — How quickly response times deteriorate, which threshold is critical?
✔ Concrete recommendations — Targeted improvement measures per identified weakness

Why DEFION - and not your CDN provider testing?
Many organizations ask their CDN or scrubbing provider to test the DDoS protection. This has a fundamental problem: the supplier tests whether their own product works — not whether your complete defense does.
DEFION is independent. We have no interest in the outcome — except that you are actually better protected. We test the entire defense chain: supplier, configuration, failover, application layer, and your own team.
Born from twenty years of fieldwork
DEFION originated from Computest Security and Incide. Our specialists have not only conducted DDoS tests — they have also handled DDoS incidents and know exactly what really goes wrong.
The three levels of DDoS resilience that we test
Technical layer — your infrastructure
Bandwidth, scrubbing capacity, firewall behavior, CDN configuration, DNS resilience. We test whether your technical defense does what the provider promises.
Application layer — your services
Web applications and APIs are often the weakest point in DDoS defense. Layer 7 attacks bypass volumetric mitigation and target specific endpoints. We test which endpoints are vulnerable and how your WAF and rate limiting perform.
Operational layer — your team and processes
A DDoS attack is also an operational incident. Does your NOC or SOC detect the attack in time? Are the correct procedures followed? Who communicates internally and externally? We evaluate your operational response and identify areas for improvement.
For organizations that prefer to outpace attackers
For which organizations is DDoS Testing essential?
DDoS tests are indispensable for organizations:
With online services where availability equals revenue — e-commerce, ticketing, online platforms
In the financial sector — banks, insurers, payment processors: availability is legally required
In critical infrastructure — energy, water, transport, telecom: NIS2 sets explicit requirements for resilience testing
That depend on public trust — government, healthcare, education: downtime has societal impact
With recent investments in DDoS mitigation that they want to validate before an attack does
After a previous DDoS attack that raises the question: are we now truly better protected?
For planned events or launches that become targets for targeted attacks
Do you want to get ahead of attackers quickly? Contact us immediately.
"New requirements from NIS2 for OT systems increase the focus on security. With DEFION, we know that we have the right expertise in-house. The collaboration was pleasant; the specialists were truly alongside us rather than opposite us." NAD Pump Station Management, manager of hydraulic engineering infrastructure
"Thanks to DEFION, we benefit from up-to-date knowledge about contemporary security threats and means to avert risks. We have peace of mind knowing we are fully supported 24/7 by their team.”
Jeroen van Stokkum Manager ICT
![[object Object]](https://assets.defion.security/api/assets/images/l7GY2Z9ip58BiQ5Bckyaz6f4Kz3KdM-w2000.webp?t=3840)
“The sector and the partners we work with maintain increasingly high security standards for IoT-products and services. Protecting the privacy of individuals in the images and the sensitivity of the information the drones collect, such as on objects in critical infrastructure, requires our security to be airtight. With Defion, we are working with a professional partner who can support us at the right level. The collaboration also fits perfectly within our strategy to deliver reliable and secure drone technology to European customers.”
Benjamin van der Hilst Co-Founder & CEO

“New requirements from NIS2 for OT systems are increasing the focus on security. With Defion, we know we have the right expertise in-house to keep our systems secure. The collaboration was easy and pleasant; the specialists truly sat next to us rather than across from us. Thanks to their openness and expertise, we are working together toward the same goal: optimal security. This gives us the confidence to face the future.”
Alexander OdijkTeam Manager

“If you look at where we were ten years ago, we’ve made enormous progress. The sense of control is greater. With Security Assurance and MDR we have set up processes and control mechanisms that allow us to limit the impact of a potential attack. The collaboration also serves as a constant reminder to maintain focus on security and set the right priorities in that area. It keeps us alert and sharp. Moreover, Defion’s specialists are highly technical and passionate about their field. That clearly shows in their services.”
Gerco VermeerDevelopment Manager

Frequently Asked Questions
Is DDoS testing legally permitted?
Yes, if it is conducted in a controlled manner and with your explicit consent. We follow strict protocols and coordinate in advance with involved providers. Everything is documented.
Can we test without risk of actual downtime?
Yes. We work with phased load buildup and agreed maximums. Tests are preferably scheduled outside peak hours. For production-critical environments, we also work with representative staging environments.
What if our provider blocks the test?
We prevent that by informing all parties in advance and obtaining permission. We fully coordinate this process.
Does the test also cover our cloud environment (AWS/Azure/GCP)?
Yes. Cloud providers have their own protocols for authorized load tests. We know these procedures and conduct tests in accordance with your cloud provider's requirements.
How long does a DDoS test take?
Intake and preparation: 1-2 weeks. Test execution: 1 day (including pre- and post-preparation time). Analysis and reporting: 1-2 weeks. Total 3-5 weeks.
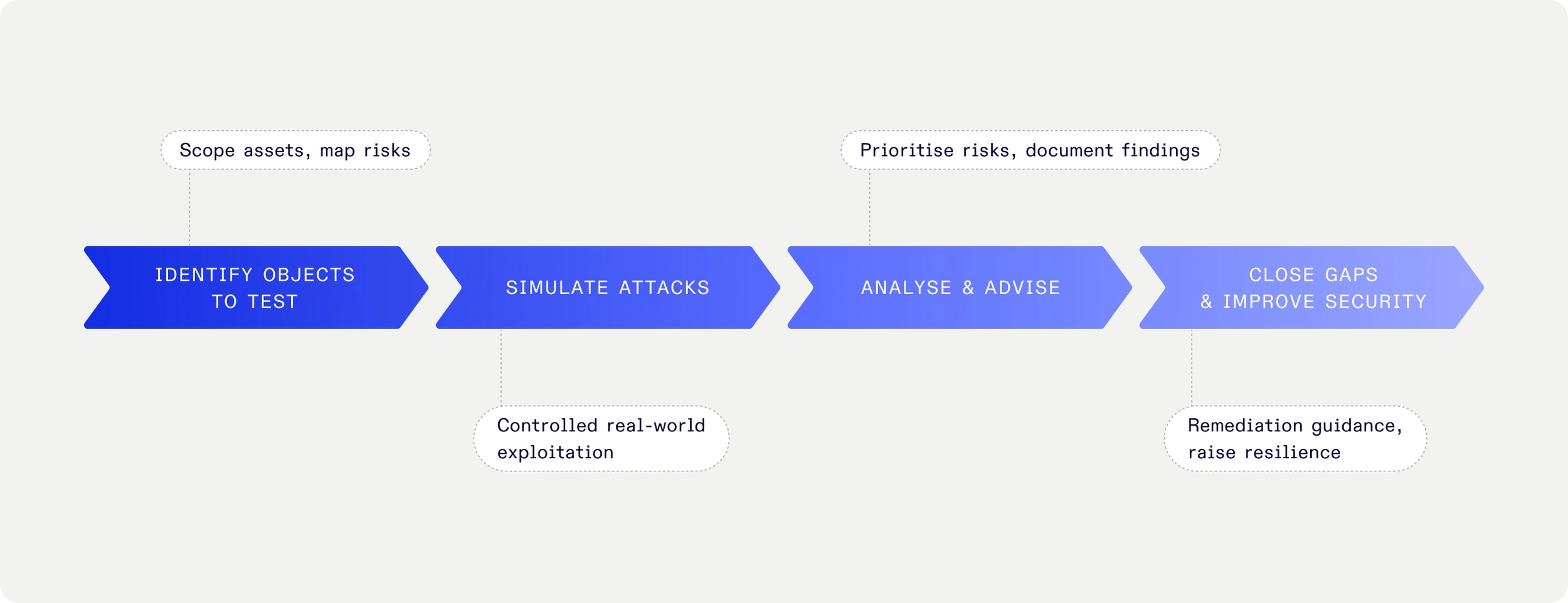
What is the difference between a DDoS test and a pentest?
A pentest looks for vulnerabilities to exploit. A DDoS test simulates availability attacks to measure your resilience. Both are complementary — together they provide a complete picture of your attack surface.
Does this comply with NIS2 requirements for resilience testing?
Yes. NIS2 requires essential and important entities to demonstrably test their continuity and resilience. A documented DDoS test with reporting is a direct fulfillment of that obligation.
Want to be sure your defense holds up?
Schedule a scope discussion — we respond within one business day
- Disaster Recovery Plan (DRP)
Downtime is more than a technical issue — it’s a business risk that directly impacts revenue, reputation, and customer trust. DEFION’s Disaster Recovery Plan (DRP) gives executives confidence that IT systems can recover quickly from outages or cyber incidents. With clear priorities, defined recovery objectives, and actionable playbooks, leadership gains assurance that critical operations can continue — even when the unexpected happens.
- DDoS Test
Simulate real DDoS attacks in a safe way. Our DDoS Test assesses system performance, team readiness, and defense effectiveness — ensuring business continuity under attack.
- Endurance Test
System stability is not defined by how fast you run a sprint — but by how well you endure the marathon. DEFION’s Endurance Test simulates continuous real-world usage to uncover risks like memory leaks and bottlenecks. Ensure your systems deliver stable performance over time.
- Load Test
When your business depends on digital services, performance under pressure is a board-level concern. DEFION’s Load Test shows executives and risk owners exactly how platforms behave at peak usage — revealing whether they can handle customer demand without disruption. The result: fact-based assurance for decision makers and clear technical guidance for improvement.
- Business Continuity Plan (BCP)
DEFION’s Business Continuity Plan (BCP) service helps organizations prepare for disruptions with tailored strategies, ensuring resilience, customer trust, and uninterrupted operations.
- Business Impact Assessment (BIA)
When a cyberattack or disruption hits, leadership needs to know **which processes matter most, what the business impact will be, and how long the organization can afford to be offline**. Without this clarity, recovery efforts risk being misaligned—protecting the wrong systems, overspending on low-priority areas, or overlooking critical dependencies.
- Stress Testing
DEFION Stress Testing pushes your systems beyond peak load to reveal bottlenecks, recovery times, and resilience gaps, before your users discover them.

Turn 24/7 security monitoring into real response capability.
Speak with our experts and learn how rapid, expert-led response transforms your security posture.
Contact usContact us