Cyber Security Assessment (CSA)
With DEFION’s Cyber Security Assessment (CSA), your organization gains a strategic, executive-level understanding of the threats it faces and the vulnerabilities that matter most. By assessing exposure across critical assets and aligning risks with business impact, DEFION delivers prioritized, actionable insights that empower leadership to strengthen resilience, optimize investments, and protect operations, reputation, and trust in an increasingly hostile digital landscape.
Cybersecurity Assessment
A Cybersecurity Assessment gives you clarity on which threats pose the greatest risk to your business, how well your current measures protect against them and where the gaps lie. Using proven security frameworks and real-world expertise, we assess resilience across people, processes and technology. You receive clear, actionable insights to prioritise improvements, reduce exposure and demonstrate control to stakeholders.
What a Cybersecurity Assessment includes
A Cybersecurity Assessment reviews technical security configurations, compliance and risk management, detection and response capabilities, and uncovers gaps so remediation and improvements can be prioritised.

What our Cybersecurity Assessment is based on
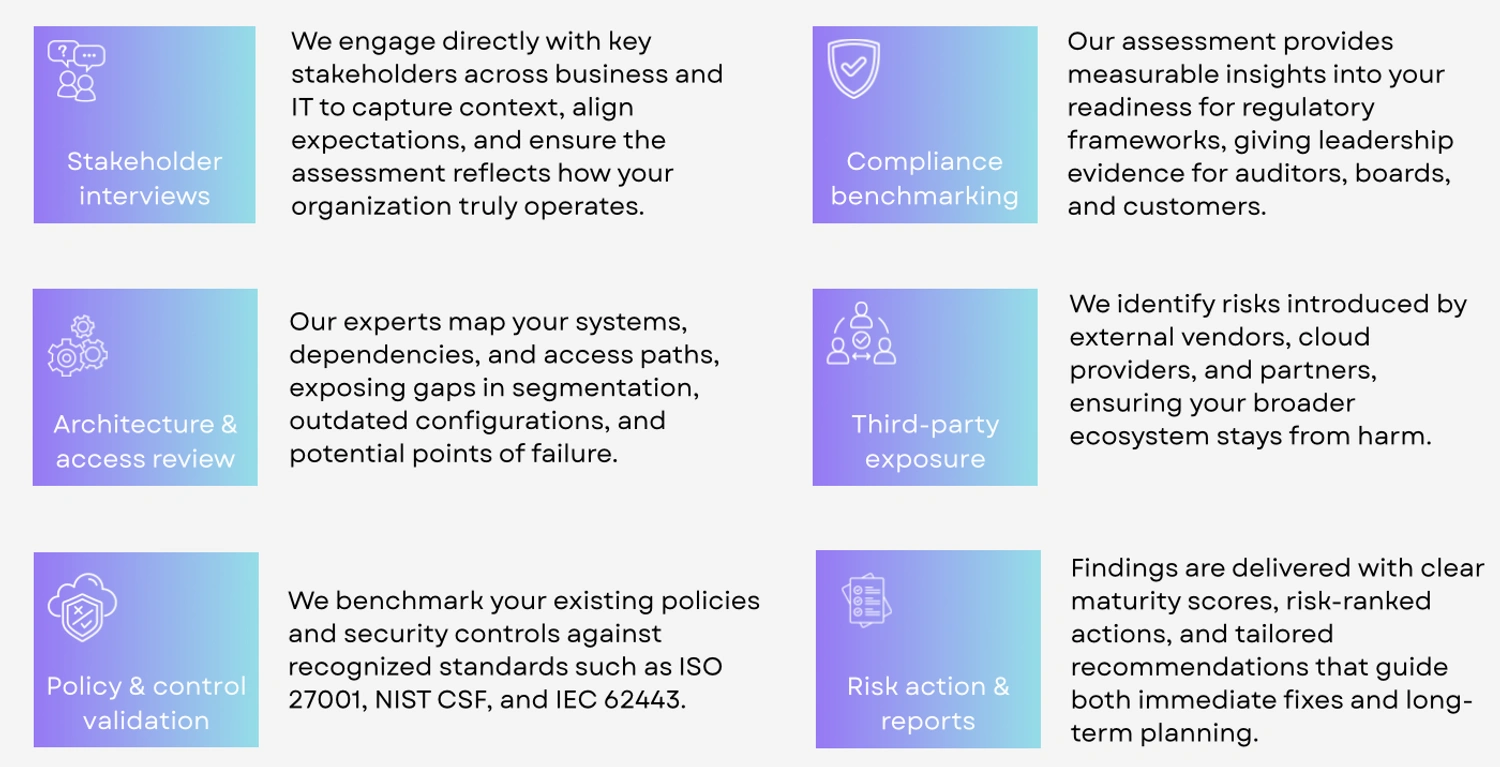
Our Security Assessment includes stakeholder interviews, policy validation, architecture and access reviews, and third-party exposure checks. It benchmarks compliance, delivers clear maturity scores and risk-ranked actions, and provides tailored recommendations to strengthen both immediate defences and long-term resilience.
What we deliver
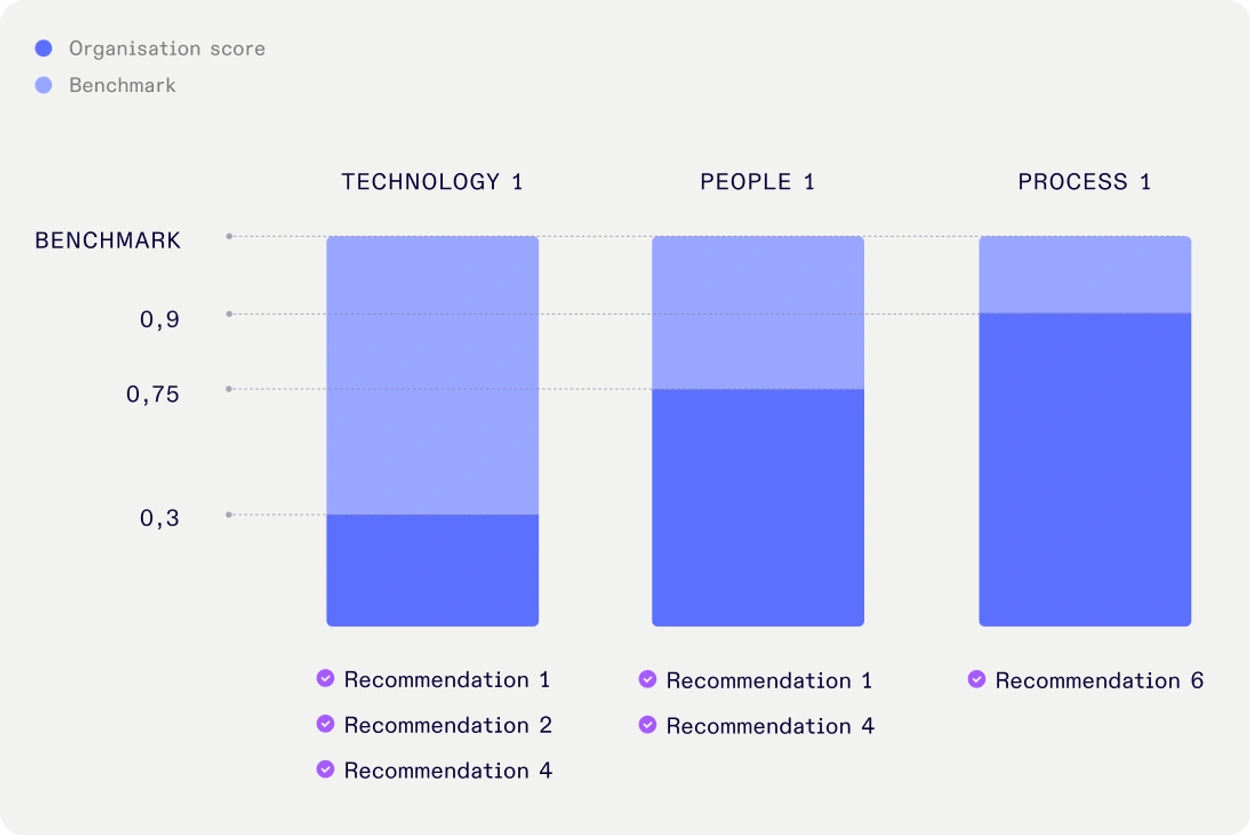
We deliver a clear threat analysis, risk profile, and improvement plan across your people, processes, and technology. The results are shared in a live presentation with concrete recommendations your teams can act on right away.
Why is a Cybersecurity Assessment essential in modern organisations?
Organisations navigate in digital environments that are more complex and connected than ever before. Expanding infrastructures, rapid cloud adoption, and growing third-party dependencies increase exposure to risks that often stay unseen. That is, until vulnerabilities are exploited and attackers have already struck. Without an encompassing outlook domains like people, proces, and technology, leadership struggles to make confident decisions on where to invest, how to prioritise, and how to demonstrate compliance to regulators, customers, and supervisory bodies. DEFIONs’ Cybersecurity Assessment closes this gap by providing a structured and independent expert view of your cybersecurity posture. The Cybersecurity Assessment provides clarity on where your cyberdefense stands and unravels risks that previously remain unseen. It’s findings are transformed into hands on guidance that enables both technical teams and executives to act with confidence. The result is not just a clear picture of your current security posture, but a deep understanding that enables the required change, accountability, and resilience across the organisation.
-
Expose false confidence by assessing whether existing security controls actually are effective, instead of relying on assumptions, incomplete documentation, or unchecked processes.
-
Align business and security by connecting risks to real impact on operations, helping leadership and technical teams focus on what truly matters.
-
Build a foundation for progress by establishing a maturity baseline that supports long-term planning, future investments, and measurable security growth.
What is a Cyber Security Assessment
Cybersecurity Assessment is a comprehensive service designed to give organizations full visibility into their security posture and maturity. It integrates market standard frameworks such as NIST CSF and ISO 27001 with the expertise of seasoned security practitioners to evaluate risks across different domains of people, process, and technology. Unlike routine audits that often scratch the surface, DEFIONs’ Cybersecurity Assessment provides a deep and practical analysis that reveals hidden vulnerabilities, uncovers gaps between policy and practice, and highlights exposures introduced by cloud integrations, vendors, and legacy systems. Every assessment is tailored to the organization’s environment and delivers both technical findings and executive-ready insights that support confident decision-making. With visual maturity scores, risk-ranked actions, and compliance benchmarking, Cybersecurity Assessment enables organisations to turn complexity into clarity and align improvements with strategic goals.
Key advantages include:
- Comprehensive outlook on the cybersecurity posture and risks across the entire organization.
- Actionable insights that help prioritize fixes and provide justification for investment.
The combination of established frameworks and practical expertise ensures that organisations not only understand where they stand today but also have a clear, evidence-based roadmap to strengthen resilience, demonstrate compliance, and build lasting cyber maturity.
# What are the main challenges in assessing security posture?
-
Limited visibility into the current security posture leaves organisations exposed to risks across systems and processes that remain undetected until they are exploited or revealed in an audit.
-
Unclear alignment with security standards and regulations creates uncertainty, as critical controls are often missing or inconsistently applied, weakening audit readiness and trust.
-
Difficulty prioritising what to fix and when overwhelms teams with findings from tools and reports, leaving high-impact vulnerabilities unresolved while effort is wasted on lower risks.
-
Fragmented documentation and legacy processes make it hard to act decisively, slowing decision-making and reducing accountability across departments.
-
No consistent view across teams or business units prevents collaboration and alignment, limiting the ability to embed security into business strategy.
-
Inability to demonstrate security maturity reduces confidence among leadership, regulators, and customers, making it harder to prove compliance or secure investment.

Turn 24/7 security monitoring into real response capability.
Speak with our experts and learn how rapid, expert-led response transforms your security posture.
Contact usContact us