
Cybersecurity Assessment
Do you know how resilient your organization really is — or do you just think you do?
✓ Independent assessment against recognized frameworks (ISO 27001, NIS2, DORA)
✓ Measurable maturity score with a concrete priority map
✓ Reporting suitable for management, board, and supervisors
Many organizations have implemented security measures. But they lack an integral, independent view of their actual security maturity. The result: investments without prioritization, compliance gaps that remain undiscovered, and uncertainty towards management and supervisors about the organization's true status.
A DEFION Cybersecurity Assessment provides that view. Objective, structured, and immediately usable.
The problem: security without an integral overview
Organizations invest in isolated measures — an EDR here, a firewall upgrade there, an awareness training — but rarely see the whole picture. Without a structural overview, the following arises:
- Investments in low-impact measures while core risks remain uncontrolled
- Insufficient alignment between IT reality and what management believes is arranged
- Compliance activities that meet legal requirements but do not improve security
- Fragmented responsibilities — no one "owns" the security position integrally
- No demonstrable basis for audit, supervisor, or cyber insurer
- Missing insight into how your position compares to industry peers
A cybersecurity assessment brings structure, measurability, and direction.
What you get with a DEFION Cybersecurity Assessment
Our assessments combine strategic analysis with technical validation:
✔ Current security level — Analysis of existing measures, governance, processes, and technical setup
✔ Risk identification — Systematic assessment of technical and organizational risks, prioritized by impact
✔ Maturity score — Measurable level on people, process, and technology against recognized models (NIST CSF, ISO 27001, CMMC)
✔ Compliance gap analysis — Testing against NIS2, DORA, ISO 27001, CRA, or sector-specific frameworks
✔ Management reporting — Clear report for management, board of directors, and external regulators
✔ Priority map — Concrete ranking of improvements based on risk impact and feasibility
✔ Implementation roadmap — Phasing with ownership, timelines, and dependencies
No generic checklist. A substantiated, organization-focused tailored assessment.

What types of assessment does DEFION offer?
Security Maturity Assessment
Systematic evaluation of your security maturity based on recognized frameworks (NIST Cybersecurity Framework, ISO 27001, CMMC). You receive a measurable starting point and a clear growth path.
Risk Assessment
Identification and prioritization of your technical and organizational risks. Which risks are critical to your business operations? Where is the likelihood of incidents highest and the impact greatest?
Compliance Assessment
Structured testing against specific standards: ISO 27001, NIS2, DORA, EU Cyber Resilience Act, or sector-specific regulations. Focused on demonstrable compliance, not just ticking boxes on paper.
Technical Security Review
Evaluation of your architecture, configurations, network segmentation, and technical security measures. Identifies technical vulnerabilities that organizational assessments do not capture.
Threat Modeling
Identification of realistic attack paths given your organization type, sector, and threat profile. Which attackers threaten you, what do they want to achieve, and how would they do it?
OT Security Baseline Assessment
Assessment of your industrial environment's security maturity — specifically focused on OT architecture, segmentation, and the convergence of IT and OT. Relevant for manufacturing, energy, water, and transport sectors.
During the intake, we determine together which combination aligns with your objectives.
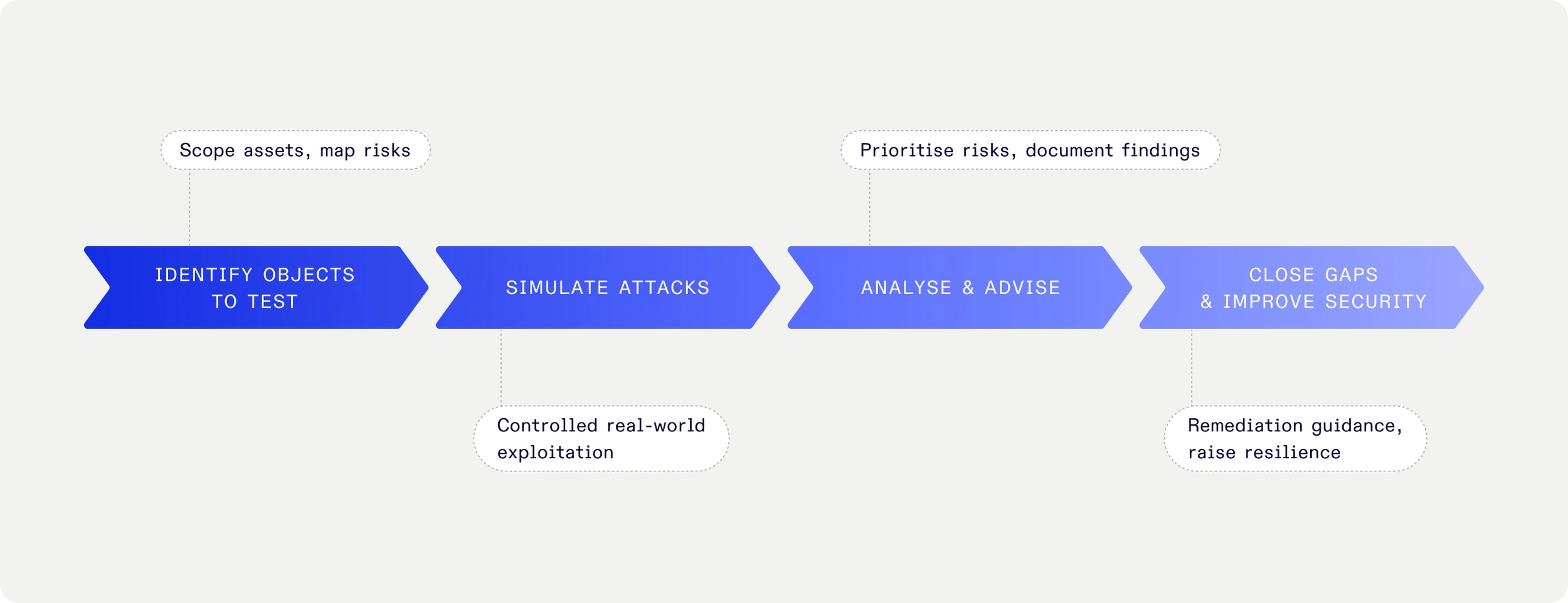
How an assessment at DEFION proceeds
-
Scope definition & objective
Together we determine the standards framework, the objective, and the involved stakeholders — IT, security, compliance, management, and any external supervisors. -
Documentation analysis
We review existing policy documents, architecture descriptions, risk registers, and previous audit reports. -
Interviews & technical validation
Structured interviews with key personnel, supplemented with technical checks to validate the actual situation — not just what is on paper. -
Scoring & prioritization
Maturity level is determined, risks are prioritized, and compliance gaps are identified. Findings are linked to business impact. -
Reporting & presentation
You receive a clear report — a technical version for IT and security, and an executive summary for management and supervisors. We present the findings in person and answer questions.
For which organizations is an assessment essential?
A cybersecurity assessment is indispensable for:
- Organizations with increasing compliance requirements (NIS2, DORA, ISO 27001, CRA)
- Boards that bear personal liability for security (NIS2) and need demonstrable insight
- Organizations that want to invest risk-driven instead of allocating budget intuitively
- Organizations that need audit assurance towards supervisors, insurers, or customers
- After an incident: understanding how it happened, and what must structurally change
- During mergers, acquisitions, or outsourcing: validating governance and security position before decision-making
- Organizations setting up a structured security program for the first time

"If you look at where we were ten years ago, we have made tremendous progress. The sense of control is greater. We have established processes and control mechanisms that enable us to limit the impact of a potential attack." FuturumShop, e-commerce client
"Thanks to DEFION, we benefit from up-to-date knowledge about contemporary security threats and means to avert risks. We have peace of mind knowing we are fully supported 24/7 by their team.”
Jeroen van Stokkum Manager ICT
![[object Object]](https://assets.defion.security/api/assets/images/l7GY2Z9ip58BiQ5Bckyaz6f4Kz3KdM-w2000.webp?t=3840)
“The sector and the partners we work with maintain increasingly high security standards for IoT-products and services. Protecting the privacy of individuals in the images and the sensitivity of the information the drones collect, such as on objects in critical infrastructure, requires our security to be airtight. With Defion, we are working with a professional partner who can support us at the right level. The collaboration also fits perfectly within our strategy to deliver reliable and secure drone technology to European customers.”
Benjamin van der Hilst Co-Founder & CEO

“New requirements from NIS2 for OT systems are increasing the focus on security. With Defion, we know we have the right expertise in-house to keep our systems secure. The collaboration was easy and pleasant; the specialists truly sat next to us rather than across from us. Thanks to their openness and expertise, we are working together toward the same goal: optimal security. This gives us the confidence to face the future.”
Alexander OdijkTeam Manager

“If you look at where we were ten years ago, we’ve made enormous progress. The sense of control is greater. With Security Assurance and MDR we have set up processes and control mechanisms that allow us to limit the impact of a potential attack. The collaboration also serves as a constant reminder to maintain focus on security and set the right priorities in that area. It keeps us alert and sharp. Moreover, Defion’s specialists are highly technical and passionate about their field. That clearly shows in their services.”
Gerco VermeerDevelopment Manager

Frequently Asked Questions
How much does a cybersecurity assessment cost?
This depends on the size of your organization, the chosen framework, and the desired depth. An intake interview is free of charge. We provide an initial estimate within one business day.
How long does an assessment take?
Typically 4-8 weeks from intake to final report, depending on scope and availability of involved parties.
How does this differ from a pentest?
An assessment is strategic and organization-focused: we evaluate policies, processes, governance, and technical setup. A pentest is technical and exploratory: we actively try to exploit vulnerabilities. They are complementary — an assessment sets priorities, a pentest validates whether the defense works.
Can we share the report with our auditor or regulator?
Yes, and we recommend it. Our reports are prepared with external stakeholders in mind.
What if we have already had a previous audit?
We take previous reports as input and focus on what has changed since then and on blind spots that were previously missed.
Does DEFION also offer guidance on implementing recommendations?
Yes. We are happy to assist with priority planning and implementation support, including CISO as a Service for organizations that need structural security leadership.
Why DEFION — and not a large consulting firm?
Technical depth and strategic advice
Large consulting firms deliver compliance reports. DEFION provides technically validated insights supplemented with strategic advice — by specialists who also perform pentests and incident response.
Vendor-neutral and without a sales agenda
We do not sell products. Our recommendations are based on your interests — not on licensing opportunities.
IT and OT
Our assessors understand both IT environments and industrial OT architectures. In sectors where IT and OT converge — manufacturing, energy, water, transport — this is distinctive.
Born from twenty years of fieldwork
DEFION originated from Computest Security and Incide. Our assessors are also pentesters and incident responders. They not only know what is theoretically vulnerable — they know what attackers do in practice.
Ready for objective insight into your actual security position?
Schedule a conversation with one of our assessment specialists — we respond within one business day
- NIS2 Readiness Assessment
NIS2 is more than a regulatory requirement — it is a strategic test of your organization’s resilience. DEFION’s NIS2 Readiness Assessment provides executives with a clear view of current gaps, prioritized actions, and a roadmap to compliance. The outcome: board-level assurance that your business can meet obligations, avoid penalties, and strengthen trust with customers, partners, and regulators.
- Cyber Insurance Advisory Services
DEFION offers independent advice on cyber insurance, working with Hienfeld, YouSure, Meijers, and Schouten Zekerheid — and trusted by CHUBB, Beazley, and AIG for Incident Response.
- DORA Readiness Assessment
The EU Digital Operational Resilience Act (DORA) reshapes how financial institutions and their partners must manage ICT risk. For executives, it is not just about compliance but about ensuring operational continuity under regulatory scrutiny. DEFION’s DORA Readiness Assessment provides a clear picture of your current maturity, identifies compliance gaps, and defines a roadmap to resilience. The result: board-level assurance that your organization can withstand disruption while meeting regulatory expectations.
- ISO 27001 Readiness Assessment
Achieving ISO 27001 certification is more than a compliance milestone — it is a signal of trust to customers, partners, and regulators. DEFION’s ISO 27001 Readiness Assessment gives executives a clear view of where the organization stands today, what gaps must be closed, and how to build a structured path toward certification. With board-level insights and actionable guidance, leadership gains the confidence to invest wisely, reduce risk, and strengthen the company’s security posture.
- CISO as a Service
For many organizations, maintaining a strong cybersecurity strategy is essential—but hiring a full-time Chief Information Security Officer (CISO) can be costly, complex, and hard to scale. That’s where CISO as a Service from DEFION comes in.
- Security Compliance Services
In today’s regulatory landscape, compliance is more than a box-ticking exercise — it is a board-level responsibility. DEFION’s Security Compliance Services help executives and risk owners translate complex requirements into actionable strategies. By aligning governance, risk, and compliance (GRC), organizations not only meet regulatory obligations but also strengthen resilience, protect reputation, and enable informed decision-making.
- Cyber Security Assessment (CSA)
With DEFION’s Cyber Security Assessment (CSA), your organization gains a strategic, executive-level understanding of the threats it faces and the vulnerabilities that matter most. By assessing exposure across critical assets and aligning risks with business impact, DEFION delivers prioritized, actionable insights that empower leadership to strengthen resilience, optimize investments, and protect operations, reputation, and trust in an increasingly hostile digital landscape.
- OT Security Baseline Assessment
Operational Technology (OT) environments are increasingly interconnected — and therefore increasingly exposed to cyber risks. For enterprises and (semi-)public organizations, understanding and improving OT security posture is critical to ensure safety, continuity, and regulatory compliance.
- Cyber Comfort Check
DEFION’s Cyber Comfort provides recurring cybersecurity maturity assessments and advisory for SMEs, insurers and insurance brokers. Continuous insight, guidance, and peace of mind.
- Security Awareness Masterclass
DEFION’s Security Awareness Masterclass equips executives and key decision makers with insights and strategies to foster a security-first culture. By connecting current threats and human behavior with organizational resilience, leaders gain the tools to reduce risk, strengthen trust, and embed security into daily business operations.
- Cyber Security Executive Services
Cybersecurity is no longer just an IT concern — it is a business-critical risk that demands executive ownership. DEFION’s Cyber Executive Services provide boards and C-level leaders with tailored guidance to navigate complex threats, compliance requirements, and investment decisions. By combining strategic insight with technical depth, we help leadership embed security into corporate governance, protect enterprise value, and inspire stakeholder confidence.
- CRA Readiness Assessment
The EU Cyber Resilience Act (CRA) sets a new bar for product security and accountability. For executives, this means not only compliance risk but also market opportunity. DEFION’s CRA Readiness Assessment gives leadership a clear view of current product security posture, identifies regulatory gaps, and defines a roadmap to compliance. The result: confidence to meet CRA obligations, protect brand reputation, and maintain competitiveness in the European market.
- Security Assurance
With DEFION’s Security Assurance, organizations transform cybersecurity from a reactive cost into a strategic enabler of business continuity. Starting with an assessment and tailored roadmap, DEFION reduces operational burden while continuously validating defenses, simulating threats, and guiding priorities through quarterly executive sessions. Delivered for a fixed monthly fee, it empowers leadership with clarity, resilience, and long-term risk reduction—making DEFION your trusted partner in sustainable security.

Turn 24/7 security monitoring into real response capability.
Speak with our experts and learn how rapid, expert-led response transforms your security posture.
Contact usContact us