Car Hacking Project Volkswagen & Audi

by Daan Keuper
Head of Security ResearchControl over the navigation system
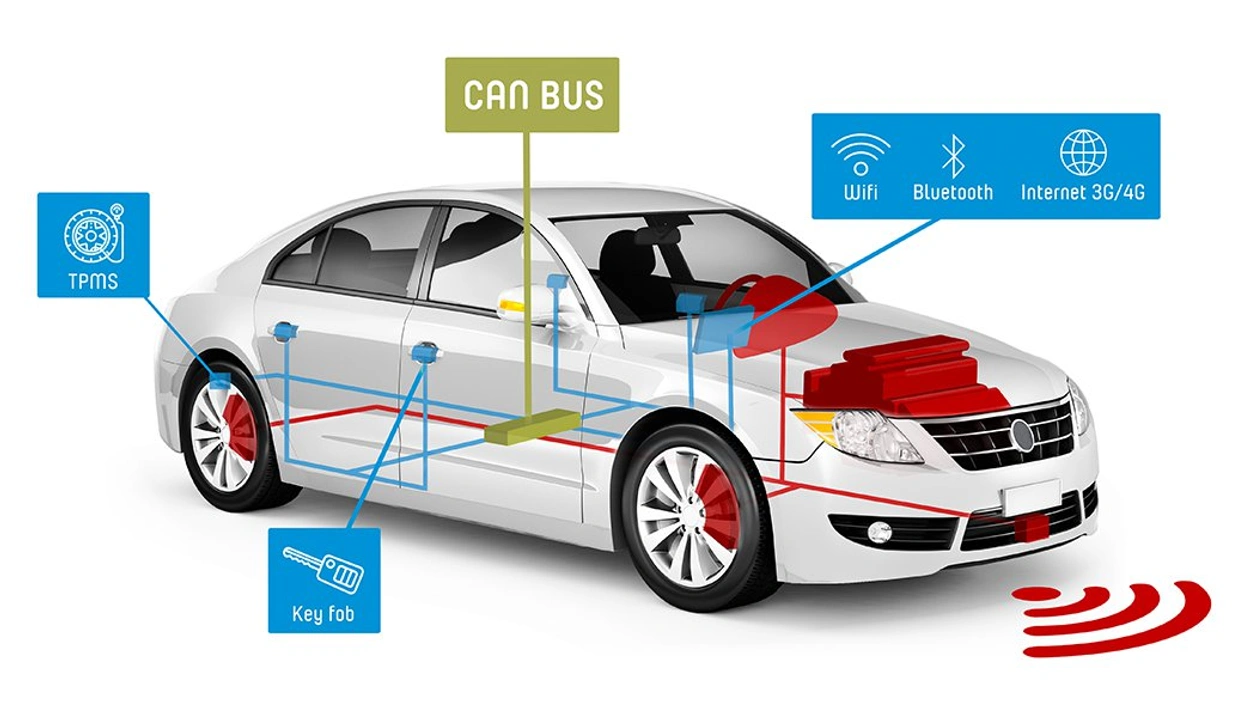
Research goal: “Can we influence the driving behavior or critical security systems of a car via an internet attack vector?”
The systems to which we were able to gain access are connected indirectly to the systems responsible for braking and accelerating. Since hacking of such systems is illegal and the intellectual property of the manufacturer is thereby infringed, it was decided at that point to stop the investigation.
Modernisation of update policy
Immediately after the discovery we reported the leak to the Volkswagen Group. They have now been able to inform us that the vulnerabilities have been solved. However, this does not mean that the danger has passed. It is, in fact, impossible to update this type of infotainment system at a distance, which means that cars already in use with this system are still vulnerable. And if you may rightly assume that a car is on average 18 years old when it is scrapped, then there are still many years in which attackers could abuse that system.
This is why we advocate modernisation of the update policy by the automotive industry, in order to make it easier for consumers to update the software systems in their cars to the most recent version. This would mean that they can always be protected against the latest threats.
Related posts



